

In the early days of the internet, gay men carved out their own corners of cyberspace like digital insurgents – IRC chatrooms, message boards, and cam-to-cam platforms became sanctuaries and sites of risk, discovery, and coded intimacy. Today, we live in a world where swipe culture and algorithmic matchmaking have replaced personal ads and forum threads. But how has the experience of gay intimacy evolved through the architectures of the web? What is gained – and what’s flattened – when desire is filtered through interfaces?
From cruising apps to hookup hubs, the erotic economy of attention in digital queer spaces has become both more efficient and more complex. And while dating apps for straight users often promise long-term love or compatibility, platforms geared toward queer users, particularly gay men, carry a different weight: they are places where identity is negotiated alongside intimacy, and where connection can be as much about affirmation as it is about gratification.
Online platforms shape how we imagine connection – not just whom we see, but how we see. On many gay-centric platforms, this translates into filtered grids of torsos, suggestive bios, and location-based rankings. These interfaces aren’t just technical tools; they are architectures of desire, coded with assumptions about availability, desirability, and performance.
In apps like Grindr, Scruff, or newer contenders, physical proximity is prioritized over compatibility, and visuals are compressed into immediate legibility. That is: you are reduced to what you can signal quickly. This opens certain freedoms (to express yourself visually, erotically, directly), but also reinforces systemic exclusions: racial preferences, ageism, body hierarchies.
Design isn’t neutral. The swipe, the grid, the disappearing photo – each action structures a kind of engagement. The body becomes a menu item. Conversation is reduced to shorthand. Emotional labor is minimized in favor of immediacy.
Search is political. Who is findable, and by what filters, reflects the value systems of the platforms themselves. Queer users, particularly trans and non-white gay men, often find themselves pushed to the margins of visibility in mainstream dating ecosystems. Even when included, they’re subject to exoticization, tokenism, or outright exclusion.
Hookup platforms tailored specifically for gay users attempt to address this by offering more fluid settings or affirming spaces for niche identities – bears, twinks, leather, dom/sub, poz, discreet, and so on. The interface becomes a taxonomy of desire, where visibility is currency, and self-categorization is power.
These platforms don’t just show you others – they show you you, reflected back through your search history, matches, and the type of attention you attract. Your desire is both the product and the profile.
The promise of queer digital intimacy also comes with real-world risks. Despite platform advancements, many users still face harassment, outing, or blackmail, especially in countries with anti-LGBTQ laws or hostile environments. GPS-based systems can be exploited. Photos shared in confidence can be weaponized.
Some platforms now incorporate panic buttons, blurred image options, or HIV status disclosure tools. But these features often address symptoms, not systems. The platform economy incentivizes engagement – not always safety.
Moreover, the assumption that queer users are “out” or publicly visible is problematic. For many, these platforms are used under conditions of secrecy, anxiety, and surveillance. This colors every interaction with a latent tension: pleasure laced with paranoia.
Yet, in all this complexity, there’s magic.
Digital queer spaces allow for experimentation not always possible offline. Users can play with identity, fantasy, kink, and relational dynamics in ways that physical spaces – bars, clubs, even Pride events – often constrain through norms or commercial pressures.
There are hookup sites and platforms that center these exploratory dynamics, resisting the mainstreamization of queer tech. One example is https://www.nearhookups.com/blowjob-near-me/ – a platform where men connect based on intention rather than expectation, and where encounter is framed not as performance but as possibility.
If digital hookup culture is here to stay, the question becomes: how can it be better? Not more optimized, but more caring. Not more efficient, but more liberatory.
What if platforms for gay and queer users were built with queerness at the center – not just in who they serve, but how they function? What if instead of mirroring heteronormative hierarchies, they invited play, ambiguity, and refusal? What if they made space for softness, uncertainty, and disclosure on your own terms?
Technologists and designers working at the intersection of queerness and code are already asking these questions. Platforms like Lex (for queer text-based dating), queer Discord servers, and even decentralized hookup networks point toward alternative futures – where connection isn’t about frictionless UX, but about respect, thrill, and consent.
To reduce queer hookup culture to casual sex is to miss the point.
It’s about networks of care, moments of affirmation, tools of self-construction. It’s about seeing and being seen. And while digital platforms are imperfect – coded with biases, surveilled, and gamified – they also carry the raw intimacy of queer futurity.
In the end, hookup culture online is not the erosion of real intimacy – it’s a mirror held up to a culture that still doesn’t know how to hold queer desire. But inside that screen, through a click or a match or a message, new possibilities still shimmer. And sometimes, that’s more than enough.
A list of recommendations, reflecting the dynamic culture we are part of, straddling the fields of art, technology and social change.
Events, Exhibitions, Open Calls, Festivals and Conferences
Art was only a substitute for the Internet | The Wrong Biennial, has been dedicated exclusively to online art and that alone makes it very relevant. For this fifth edition, Andres Manniste has invited artists who he felt were convinced that the Internet and what it provides is an art and for whom networks are critical for the development of their thinking and their work. For many the Internet is a daily routine of checking social media, listening to podcasts or music and researching material. Every living artist aware of the unlimited resources provided by communications networks is influenced by the internet. Many have associated a major part of their art process with the internet. This exhibition is a place where art can be playful and challenging – https://bit.ly/3nMIZKJ
Angels & Discounts | Exhibition by Iris Pokovec | 3 – 26 November 2021 | Aksioma | Project Space, Ljubljana | Part of U30+ production programme for supporting young artists. Angels & Discounts is an ode to consumerism and an elegy to unfulfilled dreams and lost ideals. It talks about the love-hate attitude to consumerist and popular culture and glorifies its charm and its power of hypnotising the masses, while at the same time offering a reflection on the transience of society’s collective stream of thought. It is a narrative about the search for free choice in the numb somnolence of supermarket aisles and shelves with tinned peas and preserved compotes – https://bit.ly/2ZQlSHf
NFT Culture Proof | Launches 9 am 9 Nov 2021 | Nathaniel Stern, Scott Kildall and others | A participatory performance on the Blockchain – a completely on-chain collaborative text – a collective artwork and crypto-native NFT series. NFT Culture Proof is a 32-day Blockchain performance, where every participant continuously adds to a collaborative stream of live but immutable text, which will be permanently placed on-chain. Each day, there are “writing prompts” from artists, thinkers, and writers in the cryptoverse, which will both focus and drive the texts we produce. It is the first large-scale Blockchain work of its kind, making the public ledger an active stage for collective creativity. Every text block submitted generates a unique NFT for the participant. These will also live completely on-chain, as crypto-native SVGs – https://bit.ly/3bBLfyy
Lecture 5: The City: Laurie Anderson: Spending the War Without You | 10 Nov 2021 | Exploring the challenges we face as artists and citizens as we reinvent our culture with ambiguity and beauty. Laurie Anderson presents Spending the War Without You: Virtual Backgrounds. The City is the fifth in a series of six lectures, looking at the challenges we face as artists and citizens as we reinvent our culture with ambiguity and beauty. This talk will consider teachers, activism and politics. Presented by Laurie Anderson, one of America’s most renowned – and daring – creative pioneers. Known primarily for her multimedia presentations, she has cast herself in roles as varied as a visual artist, composer, poet, photographer, filmmaker, electronics whiz, vocalist, and instrumentalist. Event by Mahindra Humanities Center at Harvard | Free event book at Eventbrite – https://bit.ly/3BvV9wd
Glitch: Aesthetic of the Pixels | Platform 101 – Vol.03 | Tehran, Iran | 5 – 12 Nov 2021 | Platform 101 is holding its third international group exhibition entitled “Glitch: Aesthetic of the Pixels”. After the great success of Vol.2, Platform 101, a nonprofit and independent art institution, is continuing the Glitch Video Art Group Exhibition in Tehran, Iran Vol.03, entitled “Glitch: Aesthetic of the Pixels”, curated by Mohammad Ali Famori, featuring 27 international glitch artists at Pejman Foundation: Kandovan – https://bit.ly/3pX2pPK
IAM Weekend | Barcelona Nov 11-13 2021 and Planet Earth: November 11-18, 2021 | Join the 7th annual gathering for mindful designers, researchers, strategists, artists, technologists, journalists and creative professionals looking to collectively envision sustainable futures for the internet(s). A week-long programme of live and pre-recorded sessions. The Planet Earth edition will feature live and pre-recorded sessions, available 24 hours across timezones, during 8 days, including the social live stream of Forum Day sessions of the Barcelona edition programme. Get access to the Planet Earth edition programme with a Week-long Pass or any Barcelona edition ticket. More info – https://bit.ly/3nVQwqr
Furtherfield at the Planet Earth Session at IAM Weekend | Nov 18th 2021 Watch live or on-demand the following pre-recorded videos: The Treaty of Finsbury Park 2025 – Interspecies Assembly (The one about biodiversity habitats) by Furtherfield + The New Design Congress + CreaTures. The Treaty of Finsbury Park 2025 – Ruth Catlow & Cade Diehm in conversation with Dr. Lara Houston. Get access to the Planet Earth edition programme with a Week-long Pass or any Barcelona edition ticket. More info – https://bit.ly/3nVQwqr
Call for Participation – Rendering Research | Deadline for submissions 14th Nov 2021 | We are seeking proposals to address how research is made public, and in this sense also to the infrastructures of research and its various systems of publishing. Organised by Digital Aesthetics Research Center, Aarhus University, in collaboration with Centre for the Study of the Networked Image, London South Bank University, Saint Luc École de recherche graphique in Brussels, and Transmediale festival for digital art & culture. APRJA is published by Aarhus University in partnership with Transmediale and hosted by the Royal Danish Library – https://bit.ly/3q0Na8w
People Like Us: Gone, Gone Beyond | Event by Barbican Centre | The Pit | 10 – 13 Nov 2021 | Watch and listen as unexpected narratives expand and unravel all at once around you. Inside this immersive, 360-degree cinematic installation, you’ll get to look far beyond the frame. Fragments of familiar and experimental films interact with song and audio clips in ever-changing, kaleidoscopic and kinetic collages. As time and space become elastic, viewers are opened to multiple meanings and perspectives by this seamless visual and surround-sound experience, with its playful and unsettling observations on popular culture. Under her artist name, People Like Us, Vicki Bennett has been evolving the field of audiovisual collage since the early 1990s, cutting up and layering found footage and archives | Tickets – https://bit.ly/3EqJX62
Tactical Entanglements: Creative AI Lab in conversation with Martin Zeilinger | 15 Nov 2021 6 pm FREE | Serpentine | TwitchOnline | A discussion panel on my book, “Tactical Entanglements: AI Art, Creative Agency, and the Limits of Intellectual Property” (meson press 2021). The event is put on by the Creative AI Lab and will be live-streamed on Twitch. Exploring issues around critical approaches to AI, digital art, and posthumanism with Mercedes Bunz and Daniel Chavez Heras (both Kings College London) and Eva Jäger (Serpentine Galleries). You can grab a free copy of Zeilinger’s book on the Meson Press publisher’s website, and a free e-reader with some additional relevant readings will be available on the Serpentine Galleries website – https://bit.ly/2Yqn6bk and https://meson.press/books/tactical-entanglements/
AI4FUTURE: OPEN CALL FOR RESIDENCIES | Deadline 15 NOV 2021 | AI4future is searching for 4 artists to work at an AI-based artwork in collaboration with young European activists to foster new urban community awareness. In recent years, Artificial Intelligence has been implemented in a number of fields functional to daily life: from those that simulate the cognitive abilities of the human being (image recognition, language automation, etc.) to the management of civil and social life (home automation, banking, self-driving vehicles, etc.) up to the economic and political organization (remote surveillance, privacy, impact on the world of work 4.0, health management, disinformation techniques, control over fundamental rights, etc.) – https://bit.ly/3bEeXTu
(re)programming: Strategies for Self-Renewal | With Eyal Weizman | 15 Nov 2021 7 pm | Aksioma | We have found ourselves at the crossroads of an existential decision: do we bring the mistakes of the enlightenment to their biological conclusion or do we develop a magical capacity to self-renew? For the 10th anniversary of Tactics & Practice, Aksioma presents (re)programming: Strategies for Self-Renewal “festival of conversations” with world-class thinkers debating key issues, from infrastructure and energy to community and AI, curated and conducted by writer and journalist Marta Peirano. The festival consists of 8 streaming events taking place every third Monday of the month throughout the year – https://bit.ly/3EDTA1n
Lorenzo Ravano: The Global South and the History of Political Thought | Online | 18 Nov 2021, 6 – 8 pm | The Critical Perspectives on Democratic Anti-Colonialism project invites you to our next Fall 2021 workshop. The program brings together faculty and students from across The New School interested in exploring the theoretical foundations and political manifestations of radical democratic and anti-colonial traditions. Ravano, Postdoctoral Fellow at Université Paris Nanterre, will be presenting his work, “The Global South and the History of Political Thought”. Anthony Bogues, Asa Messer Professor of Humanities and Critical Theory, Professor of Africana Studies and Director of the Center of the Study of Slavery and Justice at Brown University, will be commenting – https://bit.ly/3ECPVku
WhistleblowingForChange: Exposing Systems of Power & Injustice | The 25th Conference of the Disruption Network Lab | Conference and book launch | 26 – 28 Nov 2021. At Kunstquartier Bethanien – Berlin. The courageous acts of whistleblowing that inspired the world over the past few years have changed our perception of surveillance and control in today’s information society. But what are the wider effects of whistleblowing as an act of dissent on politics, society, and the arts? How does it contribute to new courses of action, digital tools, and content? This urgent intervention based on the work of Berlin’s Disruption Network Lab examines this growing phenomenon, offering interdisciplinary pathways to empower the public by investigating whistleblowing as a developing political practice that has the ability to provoke change from within | Facebook link – https://bit.ly/3o1ibXj
Unravelling Women’s Art | 25 November 6 pm – 7:30 pm | £5 | ONLINE EVENT | Join author PL Henderson and a trio of artists for an insightful discussion into what links female textile artists and the arts they produce, revealing a global and historic patchwork of assorted roles, identities and representations. Henderson’s new book, Unravelling Women’s Art: Creators, Rebels, & Innovators in Textile Arts (Aurora Metro Books) offers a unique overview of female-centric textile art production including embroidery, weaving, soft sculpture and more. Including over 20 interviews with contemporary textile artists, the books invites us into their practices, themes and personal motivation – https://bit.ly/3wxeqwr
Two Postdoc Positions in Critical Environmental Data Studies | Deadline 30 Nov 2021, Expected start 1 Mar 2022 | The Department of Digital Design and Information Studies within the School of Communication and Culture at Aarhus University (Denmark) invites applications for two postdoctoral positions in Critical Environmental Data Studies. The postdoc positions are affiliated with the research project Design and Aesthetics for Environmental Data funded by the Aarhus University Research Foundation (AUFF). The postdoc positions are full-time, two-year fixed-term positions. Design and Aesthetics for Environmental Data focus on historical and current practices of seeing, knowing, and designing the environment and the planet as data: as patterns, visualizations, projections, models, simulations, and other aesthetic objects with epistemic value. The working language of the project is English – https://bit.ly/3GGfu5P
Call for Book Chapters | Feminist Futures: From Witches to Maids to Robots and Beyond | Proposal submission deadline 15 Dec 2021 | Feminist Futures is a book all about bridges and connections! It aspires to take a look at the future, it wants to tell the story of witches, how neo-feudalism relates to the present monsters, how postcolonialism and post cold war politics brought us here when it comes to women’s rights. It is about automation and the constant repetition of the need for care without really doing it. It wants to bring these stories at the centre stage to talk about the future, to shed light on research that can lead us to what unites us and not to what divides us – https://bit.ly/3nSUsZ4
Books, Papers & Publications
Artistic Research – Dead on Arrival? Research practices of self-organized collectives versus managerial visions of artistic research | By Florian Cramer. (First published in Henk Slager [ed.], The Postresearch Condition, Utrecht: Metropolis M Books, 2021, p. 19-25). Since at least the early 20th century, artists groups have called their work “research”. Canonized examples include the “Bureau des recherches surréalistes” (“Bureau of Surrealist Research”) founded in Paris by André Breton and fellow Surrealists in 1925 and the Situationist International which, from 1957 to 1972, operated under the moniker of a research group and whose periodical had the form of a research journal. […] Today, transdisciplinary art/research collectives seem to be more common as a contemporary art practice in non-Western regions than in Western countries where art systems are more institutionalized – https://bit.ly/2ZNpjy1
Machines We Trust: Perspectives on Dependable AI | Edited by Marcello Pelillo and Teresa Scantamburlo | Experts from disciplines that range from computer science to philosophy consider the challenges of building AI systems that humans can trust. Artificial intelligence-based algorithms now marshal an astonishing range of our daily activities, from driving a car (“turn left in 400 yards”) to making a purchase (“products recommended for you”). How can we design AI technologies that humans can trust, especially in such areas of application as law enforcement and the recruitment and hiring process? In this volume, experts from a range of disciplines discuss the ethical and social implications of the proliferation of AI systems, considering bias, transparency, and other issues – https://bit.ly/3AMedWR
The Art of Activism: Your all-purpose guide to Making the Impossible Possible | By Steve Duncombe and Steve Lambert | It brings together the authors’ extensive practical knowledge—gleaned from over a decade’s experience training activists around the world—with theoretical insights from fields as far-ranging as cultural studies and cognitive science. From the United Farm Workers’ boycott movement in sixties’ California to a canal-side beach in present-day Saint Petersburg, these pages are packed with contemporary and historical case studies that have been shown to work in practice. The accompanying workbook contains fifty expertly crafted exercises to help you flex your creative imagination and hone your political tactics, taking you step-by-step toward becoming the most persuasive and impactful artistic activist you can possibly be – https://bit.ly/3CcKCr9
Whistleblowing for Change: Exposing Systems of Power & Injustice | Editor Tatiana Bazzichelli | Out 27 Nov 2021 | The courageous acts of whistleblowing that inspired the world over the past few years have changed our perception of surveillance and control in today’s information society. But what are the wider effects of whistleblowing as an act of dissent on politics, society, and the arts? How does it contribute to new courses of action, digital tools, and contexts? This urgent intervention based on the work of Berlin’s Disruption Network Lab examines this growing phenomenon, offering interdisciplinary pathways to empower the public by investigating whistleblowing as a developing political practice that has the ability to provoke change from within – https://bit.ly/3nTyZiP
Proof of Work: Blockchain Provocations 2011–2021 | By Rhea Myers | Art Editions, Forthcoming Jun 2022 | DAO? BTC? NFT? ETH? ART? WTF? HODL as OG crypto artist, writer, and hacker Rhea Myers searches for faces in cryptographic hashes, follows a day in the life of a young shibe in the year 2032, and patiently explains why all art should be destructively uploaded to the blockchain. Now an acknowledged pioneer whose work has graced the auction room at Sotheby’s, Myers embarked on her first art projects focusing on blockchain tech in 2011, making her one of the first artists to engage in creative, speculative and conceptual engagements with ‘the new internet’. This anthology brings together annotated presentations of Myers’s blockchain artworks along with her essays, critiques, reviews, and fictions—a sustained critical encounter between the cultures and histories of the art world and crypto-utopianism, technically accomplished but always generously demystifying and often mischievous – https://bit.ly/3nSpmki
Critical Theory and New Materialisms | Edited By Hartmut Rosa, Christoph Henning, Arthur Bueno | Published by Routledge, 15 June 2021 | Bringing together authors from two intellectual traditions that have, so far, generally developed independently of one another – critical theory and new materialism – this book addresses the fundamental differences and potential connections that exist between these two schools of thought. With a focus on some of the most pressing questions of contemporary philosophy and social theory – in particular, those concerning the status of long-standing and contested separations between matter and life, the biological and the symbolic, passivity and agency, affectivity and rationality – it shows that recent developments in both traditions point to important convergences between them and thus prepare the ground for a more direct confrontation and cross-fertilization – https://bit.ly/3BHvIrv
Articles, Interviews, Blogs, Presentations, Videos
The Chaos of Eros: in conversation with the programmers of Erotic Awakenings | Maria Isabel Martinez | Erotic life is a treasure we hold close until we believe its delight might multiply in the hands, eyes, ears, or mouth of another. One such place for sharing is “Erotic Awakenings,” an archive primarily containing writings hosted on the website of Toronto artist-run gallery Hearth Garage. The project is a collaboration between the gallery’s programmers Benjamin de Boer, Philip Ocampo, Rowan Lynch, and Sameen Mahboubi and writer and facilitator Fan Wu. Each piece of writing is singular in form and content, reflective of our varied erotic experiences. In an erotic moment, we might become unfastened from a solid sense of our identity, or further reminded of the body we can’t escape – https://bit.ly/3GPuONB
Artgames and interspecies LARPS with Marc and Ruth of Furtherfield | Podcast | The ReImagining Value Action Lab | “We talked about art, games, LARPs and other subversive high jinks on the latest episode of our Conspiracies and Countergames podcast.” Furtherfield disrupts and democratises art and technology through exhibitions, labs & debates, for deep exploration, open tools & free-thinking and is London’s longest-running (de)centre for art and technology whose mission is to disrupt and democratise through deep exploration, open tools and free-thinking. The ReImagining Value Action Lab (RiVAL) is a research and creativity workshop for the radical imagination active around the world and locally in Thunder Bay, Canada – https://bit.ly/3k815pn
The Digital Art Conundrum – how to evaluate digital art? | Computational Aesthetics | By Josephine Bosma | Digital devices have been part of developments in culture and society for decades, the arts included. They influenced, inspired, or even ‘co-produced’ the work of artists in performance, sculpture, robotics, sound art, and more. […] Though accurate and precise, it is not easily understandable and is a quite theoretical approach. To simplify their proposal: computational aesthetics offers a much-needed alternative to ‘traditional’ definitions of digital art as a purely technological or visual art form. It offers a broader perspective on the field – https://bit.ly/3BEKSy3
London’s ‘Square Mile’ Is One Big Monument To Slavery | By Stewart Home | ArtReview | When it comes to addressing what to do with artworks and memorials connected to historic racism and attendant issues relating to colonialism, some talk up their commitment to change, but their lack of action exposes a preference for the status quo. The City of London Corporation is the local authority that covers the capital’s international financial district. Not only does the Corporation pack more problematic memorials into its famous ‘Square Mile’ than almost any other council in the UK (or, for that matter, the world), it is simultaneously a major patron of the arts.” – https://bit.ly/3nJBm7y
Atari-style Artwork Makes the ‘Guinness World Records 2022’ Book | Dartmouth Edu | Mary Flanagan shows how games can be collaborative through a giant Atari 2600 joystick. “Space Invaders.” “Asteroids.” “Pac-Man.” In the 1980s, the Atari 2600 revolutionized the video game industry as families revelled in the novelty of playing video games on the TV at home. When she was growing up, professor, game designer, and artist Mary Flanagan says the Atari 2600 was one of her most influential digital experiences. Years later, Flanagan’s tribute to that experience, [giantJoystick], made it into the Guinness World Records 2022 as the largest joystick in the world – https://bit.ly/3pYupSZ
AI Horror Movie Wins Lumen Gold | The Lumen Prize for Art and Technology awarded its coveted Gold Award with a cash prize of US$4,000 to UK artist Nye Thompson and UBERMORGEN for UNINVITED, the world’s first horror movie for and by machines. UNINVITED is a horror film for machine networks and human-machine organisms exploring the nature of perception and realism of the unknown and the terror of angst and exhaustion within emergent network consciousness. This generative work (2018–) is a self-evolving networked organism watching and generating a recursive ‘horror film’ scenario using mechatronic Monsters – digital flesh running machine learning algorithms. The work is described by the artists as a radically new creature looking at the world, hearing the universe through millions of hallucinogenic virally-abused sensors and creating a hybrid nervous system – https://bit.ly/3CzRI98
‘It’s a game-changer for us’: Artists welcome guaranteed basic income plan | Deirdre Falvey | Irish Times | The pilot for a new basic income guarantee scheme for artists and arts workers could see “around 2,000” creative workers drawing income from March 2022, or “the beginning of April, and no later than that”, said Minister for the Arts Catherine Martin. She gave details of the pilot project, which will be backed by €25 million funding in 2022, at Wednesday’s Department of Tourism, Culture, Arts, Gaeltacht, Sport and Media budget briefing. A basic income guarantee was the top recommendation of the Arts and Culture Recovery Taskforce’s Life Worth Living report in November 2020, and the Minister said she intends to follow it “as closely as possible and to deliver a scheme that benefits artists and creative arts workers”. The three-year pilot will involve a weekly payment of €325 a week. The department later confirmed there will be no means test to take part in the scheme – https://bit.ly/2ZP73V6
Rhythm and Geometry: Constructivist Art in Britain since 1951 | Review by Bbronaċ Ferran | Studio International | An exhibition at the Sainsbury Centre captures something of the mood of the present, in its reflection on a balancing of constraint and liberation. Conceived by Tania Moore, the Joyce and Michael Morris chief curator, the exhibition draws closely on a “substantial bequest” in 2019 from husband and wife Joyce and Michael Morris, who developed a unique collection of British constructivist art from the 1950s on. As the couple were acquainted with many of the artists included, their collection was informed by their personal taste and sensibility. Its acquisition by the Sainsbury Centre opens up opportunities for new research from a historical perspective into a significantly under-studied domain of postwar practice – https://bit.ly/3q5huP3
These Companies Are Already Living in Zuckerberg’s Metaverse | By Megan Carnegie | Wired/Business | The Meta dream envisages whole companies operating in a virtual world. Many made the switch years ago—with mixed results. Facebook’s metaverse, or Meta’s metaverse, isn’t just being touted as a better version of the internet—it’s being hailed as a better version of reality. […] This space, Zuckerberg claims, won’t be created by one single company, but rather by a network of creators and developers. First problem: 91% of software developers are male. Second problem: You’ve been living in a version of metaverse for years—and, having taken over video games, it’s now coming for the world of work – https://bit.ly/3bwLNWn
Crofton Black – How does the world work? | Exposing the Invisible | Podcast | Crofton Black ended up as an investigator almost by chance. With a background in English Literature and Medieval and Renaissance philosophy, he took an unexpected turn into investigating secret prisons and extraordinary renditions. He is a writer and investigator. He is co-author of Negative Publicity: Artefacts of Extraordinary Rendition and CIA Torture Unredacted, and works on technology and security topics for The Bureau of Investigative Journalism in London. Before this he was a history of philosophy academic, specialising in theories of knowledge and interpretation. He has a PhD from the Warburg Institute, London and was a Humboldt Fellow at the Freie Universität Berlin – https://bit.ly/2ZIT1nO
Kirill Medvedev in prison (Moscow, Russia) | An international well known muscovite poet, translator, publicist, activist and community organizer, co-founder of Arkadiy Kots combat-folk band, a long term Free Home learner, has been arrested along with other activists. They were defending a courtyard adjacent to Sretenka street from oligarch Deripaska’s development of an unlawful construction, a luxury apartment hotel rising right on the site of historic buildings from the 18th century – despite the protests of the local residents the activists were aggressively attacked by the police and kept in the police station for 24 hours awaiting the court hearing. As the excavation continues, they are imprisoned at spetspriyomnik nr-r. 1 and 2 already for 5 days. Since long Kirill is engaged in the defence of peoples land and territories defence, against extractivism, real estate development and criminal waste dumps – https://bit.ly/3mw3uvA
Image: Hydar Dewachi. Image Courtesy of Furtherfield. View from the People’s Park Plinth Voting Weekend (14 -15 August 2021), Furtherfield Gallery, Finsbury Park.
The FurtherList Archives
https://www.furtherfield.org/the-furtherlist-archives/
A list of recommendations, reflecting the dynamic culture we are part of, straddling the fields of art, technology and social change.
Events, Exhibitions, Open Calls, Festivals and Conferences
Trouble In Outer Heaven: Portable Ops Plus | Southwark Park Galleries | 15 Sep – 31 Oct 2021 | The exhibition focuses on the influence and fandom of Metal Gear Solid, one of the most popular video game franchises of all time. Larry Achiampong, Joseph Buckley, Kitty Clark, Sam Keogh, Hardeep Pandhal, Adam Sinclair and Jamie Sutcliffe. Curated by Jamie Sutcliffe. Featuring The Diamond Dogs Educational Unit: Uma Breakdown, Petra Szemán, Zara Truss Giles. Exploring the unnerving possibilities of biogenetic cloning and military espionage; off-shore para-states and the formation of private task forces charged with seizing power from the world’s collapsing democracies, its once bizarre mythos feels disturbingly appropriate to the world in 2021 – https://bit.ly/3zS4spw
The 7th Athens Biennale ECLIPSE | 24 Sep – 28 Nov 2021 | Co-curated by Omsk Social Club and Larry Ossei-Mensah under the artistic direction of Poka-Yio. The exhibition features artists based in North and South America, the Caribbean, Africa, and Europe, many of whom will be exhibiting in Greece for the first time. The exhibition title highlights the obscured perspective of reality caused by the constant state of flux we are experiencing in our society now. ECLIPSE engages the social, political and spiritual changes of today’s global construct and in Athens itself, as a rising metropolis located at the intersection of Europe, Asia and Africa both physically and historically – https://bit.ly/3lViLVm
KIBLIX 2020–2021: Virtual Worlds Now, part II | KIBLA PORTAL | 1 Oct – 30 Nov 2021 | The group exhibition is rounded off with additional artistic works that experiment with digital and extended reality (XR) media. The exhibition will take you through a computer-generated video Delusional Mandala by Lu Yang, an artificially intelligent robot Amygdala with the Calyx installation by Marco Donnarumma, a digital fashion collection DEEP by Amber Jae Slooten and The Fabricant, a mixed-reality installation HyperBody Portal: Stratholme. Go Stop by Pete Jiadong Qiang, Spacemen R My Friended by Tony Oursler, a sensual experience of poetry and dance in virtual reality Nightsss by Weronika M. Lewandowska and Sandra Frydrysiak, an interactive intermedia installation Time of Flight by the Compiler Group, a video game What Is Your Truth? by Dorijan Šiško and Sara Bezovšek, a world in VR for platform Sansar MetaGarden: Sphere5 by Tanja Vujinović and the first-person point of view 3600 video Seeing I – The Other by Marko Farid. List of participating artists is in here –> https://bit.ly/3zT31Hh A post about it on IG: https://bit.ly/3ASjXPG
The Unmoving show | Ongoing | An open, interactive, partly performative show waiting for your contribution | Bjørn Magnhildøen | Digital exhibition with the subtitle “a psychogeographical drift in the matrix” is a critique of attention hacking and self-consumption. The exhibition is shaped as a continuous, unpredictable and erratic stream of orientation/awareness based on the works and their metadata/surroundings. The artistic content is based on invitation, open call, and open curation. The show is open for submissions of works before and during the exhibition. The scripted framework is also subject to change in the period; this adds to the performative aspects of the show. See it here – https://unmoving.show/ and at the One-Off Moving Image Festival (One second videos.) – https://noemata.net/one-off/ and, both are part of The Wrong biennale #5 – https://thewrong.org/
Liminal Territories | When AI and NFTs meet Art History | Pal Project | 5 Oct – 20 Nov 2021 | Group exhibition from Conceived by the curator Filippo Lorenzin. It brings together 15 international artists working on the interaction between art and new technologies. The exhibition proposes a new perspective on the current trends in digital art by addressing the broader historical and artistic contexts that allow us to look at GIFs and 3D scans as works of art. The exhibition is an opportunity to learn about the art practice of contemporary creatives who use cutting-edge technology such as 3D printing, AI-generative processes and digital modelling to explore reality in ways that, to various degrees, pay homage to art styles and movements of the past. By investigating the distinct creative approaches of a group of selected international artists, the exhibition offers a public used to enjoying traditional artworks a chance to learn about the most interesting contemporary trends in art. List of presented artists: Rosana Antolí, Robbie Barrat, Jim Campbell, Carla Gannis, Guildor, Auriea Harvey, Luna Ikuta, Jono, Sasha Katz, Yuma Kishi, Paul Pfeifferl, Jan Robert Leegte, Helena Sarin, Edgar Sarin, aurèce vettier – https://bit.ly/3AVwTV1
Critical Engineering Working Group EXHIBITION: Decoding Black Magic. Interventions in Infrastructure | Piksel Festival 2021, 15 November – 12 Dec 2021 | Featuring works by Bengt Sjölén, Danja Vasiliev & Julian Oliver. The Black Book of Wireless is intended to be a book of the dark magic that antennas and radios are with pages that are circuits and PCB trace antennas (copper traces on PCB material) and of which some examples are shown in this iteration. The more obscure parts of this are things that are not fully understood or even if you can model and simulate how you think they will behave you have to try them out to see how they actually behave – https://bit.ly/3kcSdOm
Open Screen 2021 | Arebyte | A yearly programme for artists working online that self-identify as disabled. Developed in partnership with Shape Arts, the open call welcomes artists who use digital tools to their advantage, overcome barriers, criticise matters of inclusivity within technology, or everything in between. Tilly Prentice-Middleton and Uma Breakdown are the two artists selected by the judging panel for 2021 out of the 53 proposals submitted to the open call. Over the span of two months, Tilly and Uma get curatorial support to develop online work that responds to Realities, arebyte’s 2021 theme to go live on arebyte on Screen at the end of September – https://bit.ly/3ianf9C
Packaged for pleasure | Brought to you by Terminal – Seekbeak | A virtual cabinet of curiosities that exists as both a single digital work and a collection of individual pieces, The Terminal: Human Shaped Whole is a mise-en-abysme of digital art turned inside out. The interactive installation gives an ironic sense of claustrophobia: digital technology promises unlimited digital space and yet everything feels compressed as if the weight of virtual reality is collapsing on itself. The Terminal: Human Shaped Whole, Directed by Jason Isolini, featuring work by Bob Bicknell-Knight, Ian Bruner, Joshua Citarella, Jessica Evans, James Irwin, Claire Jervert, Kakia Konstantinaki, Angeline Meitzler, Erin Mitchell and Neale Willis, curated by Off-Site Project – https://bit.ly/39LLW7A
Difference Machines: Technology and Identity in Contemporary Art | 16 Oct 2021 – Jan 16 2022. Albright-Knox Northland | Oppression is systemic—that is, built into the fabric of our society. Even our technologies are not neutral: as many scholars and activists have shown, they are shaped by the biases and agendas of their creators. New digital tools (including facial recognition systems, search algorithms, and databases) created by corporations and governments reflect prejudices based on our collective identities. These tools are then used in ways that contribute to existing inequalities. For example, biased programs may discriminate against disabled people in job interviews, suggest harsher sentences for Hispanic defendants, and deny medical care to Black patients. The earliest computers were called “difference engines,” as they were used to calculate the differences between numbers. Today, computers are machines used to encode the differences between us. This exhibition is organized by University at Buffalo Professor Paul Vanouse and Albright-Knox Assistant Curator Tina Rivers Ryan – https://bit.ly/2Y5uXuc
To Exhibit- · Not to Expose · To Expose · Not to Exhibit | 24 Sept 2021 – 1 Sept 2022 | Under the title To Exhibit – Not to Expose – To Expose – Not to Exhibit, we present the first cycle of programming of the new Santa Mònica. The exhibition orbits around a series of questions that derive from the very processes of deconstruction and reconstruction of an arts centre in the institutional, architectural and symbolic spheres. The first major exhibition of the new Santa Mònica reveals and questions exhibition mechanisms: the physical but invisible ones, and the immaterial ones that remain in the shadows by their very nature. The technology (high and low) that hides behind the works, the architectures behind the props, the spotlights… All are exposed – https://bit.ly/3zUYrZ6
Black Atlantic: Sensing the Planet | 29 – 31 October 2021 | Dartington, Devon, UK | A 3-day gathering at Dartington from 29-31 October, will see leading UK cultural institutions Serpentine, the Royal Court Theatre, UCL’s Sarah Parker Remond Centre for the study of racism and racialisation and Dartington Trust launch Black Atlantic, a new decolonial arts partnership that aims to strengthen the role of arts and culture in advancing social and climate justice. Sensing the Planet will highlight issues of race and environmental harm as well as the role played by the UK, and of the southwest of England in particular, in histories of slavery, empire and climate breakdown. It will also champion the role of interdisciplinary culture in imagining new futures built on principles of sustainability and justice, bringing together leading decolonial thinkers, artists and activists including headline speakers Paul Gilroy, Ruth Wilson Gilmore, Alexis Pauline Gumbs and Philippe Sands QC – https://bit.ly/39Sgp40
Books, Papers & Publications
Museums and the Working Class | Edited By Adele Chynoweth | Routledge | Museums and the Working Class is the first book to take an intersectional and international approach to the issues of economic diversity and class within the field of museum studies. Bringing together 16 contributors from eight countries. As part of the push for museums to be more accessible and inclusive, museums have been challenged to critically examine their power relationships and how these are played out in what they collect, whose stories they exhibit and who is made to feel welcome in their halls. This volume will further this professional and academic debate through the discussion of class – https://bit.ly/3m1xzBR
Mixed Forms of Visual Culture: From the Cabinet of Curiosities to Digital Diversity | By Mary Anne Francis | Bloomsbury | The book celebrates and seeks to understand the overlooked appearances of hybrid forms in visual culture; artefacts and practices that meld or interweave incongruous elements in innovative ways. And with an emphasis on the material aspects of such entities, the book adopts the term ‘mixed form’ for them. Crucially, Mixed Forms of Visual Culture relates its phenomena to the emergence of the division of labour under capitalism and addresses the shifting relationships between art and life, when singularity and uniformity are variously valued and dismissed in the two arenas, and at different points in history – https://bit.ly/2XRzYXe
Media and Management | Authors: Rutvica Andrijasevic, Julie Yujie Chen, Melissa Gregg, and Marc Steinberg | An essential account of how the media devices we use today inherit the management practices governing factory labor. Drawing on rich historical and ethnographic case studies, this book approaches key instances of the industrial and service economy—the legacy of Toyotism in today’s software industry, labour mediators in electronics manufacturing in Central and Eastern Europe, and app-based food delivery platforms in China—to push media and management studies in new directions. Media and Management offers a provocative insight on the future of labour and media that inevitably cross geographical boundaries. Meson Press – https://bit.ly/3D1nbRk
Critical Meme Reader: Global Mutations of the Viral Image | Edited by Chloë Arkenbout, Jack Wilson and Daniel de Zeeuw | Beyond the so-called ‘Alt-right’ and its attendant milieus on 4chan and Reddit, memes have passed the post-digital threshold and entered new theoretical, practical, and geographical territories beyond the stereotypical young, white, male, western subject. As they metastasized from the digital periphery to the mainstream, memes have seethed with mutant energy. From now on, any historical event will be haunted by its memetic double. Our responses to memes in the new decade demand an analogous virtuality. This Critical Meme Reader features an array of researchers, activists, and artists who address the following questions. What is the current state of the meme producer? What are the semiotics of memes? Institute of Network Cultures – https://bit.ly/3CWaKq0
Gertrude Stein: The Complete Writings (2017) | Monoskop | This chronological list of her writings was revised and updated by Robert Bartlett Haas and Donald Clifford Gallup in 1941 (Yale University Library, New Haven), extended by Julian Sawyer in 1948 (Bulletin of Bibliography), and updated again by Richard Bridgman in 1970 (Gertrude Stein in Pieces, Oxford University Press), which, with some additions, forms the basis of this anthology. All texts have been formatted to resemble the original (and often quite idiosyncratic) layout as closely as possible – https://bit.ly/3zUrigp
Articles, Interviews, Blogs, Presentations, Videos
The Original Cryptoartist was also the Original Cryptoleftist | Interview with Rhea Myers | The Blockchain Socialist | An artist, hacker and writer originally from the UK now based in Vancouver. Her work with technology and culture produce new ways of seeing the world as it unfolds around us. She’s been involved in the blockchain art world probably for as long as it has existed and has had her art recently featured in Sotheby’s first NFT auction sale. “What I’ve found incredible about her work is how prescient it was around art and includes the first writings attempting to synthesize blockchain with left politics. She is one of the authors who contributed to the Artists Re: Thinking the Blockchain book published by Furtherfield”. – https://bit.ly/3ETJbiU
CLASSES | Libby Heaney, 2021 | A video essay exploring the entanglements between machine learning classification and social class(ification). The artwork takes place in a simulated model of a London council estate, where Heaney lives. Machine and human voices playfully narrate aspects of Heaney’s in-depth research into accented speech recognition, natural language processing* and public space surveillance, to understand how historical and cultural biases around social class are being translated into code and how this affects people’s material conditions – https://bit.ly/3zHCbSj
The BLACK BOX EAST project | Berlin Gazette | Video presentations | As a starting point for a critical inquiry of “post-communist” spaces at large in East Germany, with a focus on black boxed processes of privatization and globalization. The project intends to look at these very processes from different international perspectives, rethinking “the East” from within, against, and beyond national borders. Participants from more than 30 countries are invited to embark upon an analogous exploration and to collectively create points of intersection. The overall aim is to generate common paths of transnational discourse and struggle by challenging the BLACK BOX EAST as a predatory capitalist system of excessive economic and political dispossession that can no longer be obscured or ignored – https://bit.ly/3ENFIlU
YouTube suspends filmmaker Oliver Ressler’s account without warning | Art-leaks.org | The YouTube account of the Austrian filmmaker and artist Oliver Ressler was suspended last Thursday for alleged “repeated violations”. YouTube issued Ressler with a message warning that “spams, scams or commercially deceptive material are not allowed on YouTube”. The artist says that no such material had been uploaded to his channel, that no prior warnings about such violations had been received and accuses the video-sharing platform of censoring his work – https://bit.ly/3lZmEZw
Beeple and Jordan Wolfson | Dialogues: The David Zwirner Podcast | Society & Culture | Apple Podcasts | When Mike Winkelmann, now widely known as the digital artist Beeple, sold an artwork at Christie’s for $69 million in March 2021, it shocked the art world—and created an escalating interest in and market for NFTs, digital art using blockchain technology that allows the work of digital artists like Beeple to be collected for the very first time. But the high-stakes prices also brought two parallel art worlds—the traditional one of galleries and museums, and the growing online community of digital artists—crashing into each other. In this provocative conversation, Beeple and Jordan Wolfson hash out the relationship between the two and ask: Where do we go from here? https://apple.co/3oaMs7G
Seeing Through The Debris | Jay Springett | “The basic idea of the ‘Breakaway Civilization’ is simply that you have a secret group, a classified group of people, with access to radically advanced technology, radically advanced science, and they just don’t share it with the rest of the world. One scientific breakthrough leads to another, and that leads to another and so on. So the next thing you know, you’ve got a separate group of humanity that is vastly far beyond the rest of the world.” https://bit.ly/39FO94v
Should We De-Extinct Woolly Mammoths? | By Alex Pearlman | Geneticist George Church broke my corner of the internet again last week when it was announced that his company Colossal, co-led by serial entrepreneur Ben Lamm, raised $15 million for a very controversial de-extinction project targeting the woolly mammoth. This news was another wonderful example of media sensationalism, and hundreds of explosive headlines made it seem like Jurassic Park: Siberia! is imminent. The thing is, that’s not accurate. It’s not a de-extinction project, it’s a hybridization project that could produce a cold-resistant Asian elephant. Can we say that the existence of one or two hybrid elephants is the same as resurrecting an extinct species? – https://bit.ly/2ZDh8nR
Image: DEEP by Amber Jae Slooten and The Fabricant. Digital-only fashion collection, video, 2018. Part of the KIBLIX 2020–2021: Virtual Worlds Now, part II, 1 Oct–30 Nov 2021.
The FurtherList Archives
https://www.furtherfield.org/the-furtherlist-archives/
A list of recommendations, reflecting the dynamic culture we are part of, straddling the fields of art, technology and social change.
Events, Exhibitions, Festivals and Conferences
Data Dating | Exhibition Wednesday 15 January – Sunday 1 March 2020 | What does it mean to love in the Internet age? How are digital interfaces reshaping our personal relationships? What do new technologies imply for the future of the romantic sphere? How do screens affect our sexual intimacy? Are the new means of connection shifting the old paradigms of adult life? The advent of the Internet and smartphones has brought about a split in the romantic lives of millions of people, who now inhabit both the real world and their very own “phone world” | Artists: Addie Wagenknecht & Pablo Garcia, !Mediengruppe Bitnik, Ashley Madison, Angels at Work in London, VR Hug, Tom Galle, Moises Sanabria, John Yuyi, Antoine Schmitt, Olga Fedorova, Adam Basanta, Jeroen Van Loon, Thomas Israel | Watermans Art Centre, London – https://bit.ly/2unO6ZX
Querying the Archive | Hosted by MayDay Rooms | Thursday, 13 February 2020 | London | An on-going series of workshops around our archival platform leftove.rs, which will look at the different ways we can open up this online collection material and the technical processes between it. We want to think through that kind of strategies, queries and categories will help us navigate something that is both an database and resource of radical history. The first session we will be learning about the platform and mapping the collection by pooling our knowledge of radical histories of dissent to help us think about how we search, input and categories this large collection of material. https://leftove.rs
The Habitat of Time | Curated by Julie Louise Bacon | Arts Catalyst | Thu 20 February 2020 – Sat 14 March 2020 | The project focuses on the way that time as a medium shapes our perception of life, the structure of societies, and the vastness of the physical world. The artworks featured in the exhibition propose a rescaling of human time and expose its deep interrelations with the diversity of the more-than-human realm, moving through the geological, technological, biological and cosmic. In the 21st century, the instability of globalisation, the speed of digital technologies, and the transformation of knowledge are generating rapid shifts in time | Featuring: Eva Nolan, Thomson & Craighead, Robert Andrew, Lucy Bleach, James Geurts, Josh Wodak – https://bit.ly/2uo2Sjv
Pre-histories and Futures of Machine Vision | Friday, 28 February 2020 | V&A, London | How do machines see? From autonomous vehicles to deep fakes, machine vision is changing contemporary life. Join curators, artists and scholars to discuss the impact of AI technologies on the past, present and future of art. Explore early moments in the development of computer art and machine vision, from the mid-1960s onwards in the home of the UK’s most important historic computer art collection. Join contemporary artists, designers and curators considering the aesthetic and political implications of contemporary computer vision and machine learning technologies. Speakers include digital scholars Zabet Patterson (Stony Brook) and Joel McKim (Birkbeck), V&A curators Douglas Dodds and Natalie Kane, and contemporary artists Anna Ridler and Alan Warburton | 10.30 – 17.00 | Hochhauser Auditorium, V&A South Kensington – https://bit.ly/371PYVM
QUANTUM: IN SEARCH OF THE INVISIBLE | From March 5 until May 31, 2020 | An international art exhibition exploring the world of quantum physics, through works created by artists resulting from their encounters with researchers at CERN, Geneva | Featuring ten commissioned artworks by internationally renowned artists, which rethink scientific research and facts to explore states of being and the very possibilities of reality. These works question how much we really know about the world around us, and how we may begin to discover new aspects by taking a different perspective | Brussels, Belgium – https://www.imal.org/en
Three Acres And A Cow | Hosted by Three Acres And A Cow and 3 others | ‘Three Acres And A Cow’ connects the Norman Conquest and Peasants’ Revolt with current issues like Brexit, fracking, the housing crisis and food sovereignty movement via the Enclosures, English Civil War, Irish Land League and Industrial Revolution, drawing a compelling narrative through the radical people’s history of England in folk song, stories and poems. Part TED talk, part history lecture, part folk club sing-a-long, part poetry slam, part storytelling session… Come and share in these tales as they have been shared for generations. Featuring Robin Grey and Rachel Rose Reid | 12 March 2020 – http://threeacresandacow.co.uk
Workshop: Subvertising for the right to housing | March 26, 2020 @ SUPERMARKT BERLIN | With Steal This Poster (Subvertising Collective IT/UK) and others. These workshops show us how subvertising offers a creative way to rewrite the narrative about the housing market in the streets where gentrification operates. Outdoor advertising is the most emblematic form of consumerist propaganda. It privatises sections of public spaces with the purpose to conditioning mass behaviours imposing specific narratives. How can we untangle those narrations? And how can we take over those spaces subtracted from the public realm for private interests? | registrations open soon | sign up for the newsletter – https://bit.ly/2OqppD2
EVICTED BY GREED: Global Finance, Housing & Resistance | Uncovering how ghostly shell companies and real estate speculation evict real people from their homes – and what to do about it | Investigations on how how speculative finance drives the global and local housing crisis, and gathers experts & activists from around the world to share and find counter-strategies | The Conference, March 27-28, 2020, Studio 1, Kunstquartier Bethanien | Disruption Network Lab – https://bit.ly/2S2SEya
Books, Open Calls, Papers & Publications
Open Call – Science Gallery London | Inviting expressions of interest for projects to become part of the forthcoming AI & Ethics season. Whether your application is art, scientific inquiry, or a combination of these, we are looking to work with individuals and groups who are critically exploring ethical issues around the development and implementation of artificial intelligence (AI), particularly (though not exclusively) within the context of healthcare | Open from 31st January 2020 to 23rd February 2020 – https://bit.ly/2Ut377q
Open Call – URgh! zine #1 on Alternative Art Education | DEADLINE Friday, 21 Feb 2020 | Submissions are open for the first issue of URgh! We welcome contributions that explore and document alternative art education within self-organised, DIY, peer-led art schools and collectives, to extend the existing research and amplify the movement. A new zine on precarious labour dreaming up alternative economies at the coalface of the art educational creative industrial complex. The first issue will be launched on Saturday, 21 March 2020 at the Festival of Alternative Art Education 2020 at Conway Hall. https://videomole.tv/urgh-zine/
Art Meets Radical Openness 2020 – OPEN CALL: Of Whirlpools and Tornadoes | 20th – 23rd of May 2020 | Deadline: Monday 24.02.2020 | AMRO is a biennial community festival in Linz that explores and discusses new challenges between digital culture, art, everyday life, education, politics and activism. The 2020 edition of the AMRO festival is characterized by reflections upon the “centripetal” and “centrifugal” dynamics of acceleration visible in contemporary society and the ways artistic practice, activism and radical thinking can engage with it – http://radical-openness.org/en
Technological Sovereignty: Democratising Technology and Innovation Green Paper | Within DiEM25, by crowdsourcing collective knowledge have identified three key ways to achieve Technological Sovereignty. They try to define the issues, and provide short, medium and long term solutions, based on two processes: Regulation and Renewal. And we need to establish the conditions for social innovation and democratic societal transformation – https://internal.diem25.org/en/vote/205/public
Culture, Technology and the Image: Techniques of Engaging with Visual Culture | Edited by Jeremy Pilcher | Culture, Technology and the Image explores the technologies deployed when images are archived, accessed and distributed. The chapters discuss the ways in which habits and techniques used in learning and communicating knowledge about images are affected by technological developments. The volume discusses a wide range of issues, including access and participation; research, pedagogy and teaching; curation and documentation; circulation and re-use; and conservation and preservation | Intellectbooks – https://bit.ly/2v9CFoF
Hacking Diversity: The Politics of Inclusion in Open Technology Cultures | By Christina Dunbar-Hester | Hacking, as a mode of technical and cultural production, is commonly celebrated for its extraordinary freedoms of creation and circulation. Yet surprisingly few women participate in it: rates of involvement by technologically skilled women are drastically lower in hacking communities than in industry and academia. Hacking Diversity investigates the activists engaged in free and open-source software to understand why, despite their efforts, they fail to achieve the diversity that their ideals support | Prince University Press – https://bit.ly/2SlvCBl
Call for Papers – Media Theory, Media Fiction, and Infrastructures Beyond the Earth | Today, established space agencies are struggling with national funding, and numerous countries are starting ambitious space programs, and private companies and individuals are building innovative space plans and technologies. The current socio-political configuration offers thinkers and practitioners new opportunities by which to intervene in how we envision and inhabit the cosmos. Media Theory, Media Fiction, and Infrastructures Beyond the Earth is a two-day workshop May 7-8, 2020 at University of Toronto, Mississauga that will investigate space exploration and inhabitation from the point of view of media studies | University of Toronto Mississauga, USA – https://bit.ly/383z623
Call for proposals – (Infra)Structures | 4 – 5 June 2020 | Centre for Postdigital Cultures annual conference | Coventry University, UK | Proposals for its 3rd annual conference on infrastructures | This conference takes interest in infrastructures as an invisible system of meaning-making and a mode of structuring people and knowledge, in the institutional contexts and conditions of this structuring, as well as in possible models of intervening in these very structures. By doing so, we hope to interrogate the potential of making infrastructure visible – remarkable – as a means of speaking to power. We are interested in exploring what new ways of understanding, developing, reconfiguring or hacking infrastructures might be possible if we focus on their radical potential – https://bit.ly/31rd1rC
Articles, Interviews, Presentations, videos
Poetry v. the Body Politic: writing a political movement | Excerpts from a dialogue on the relationship between poetry and politics in Iran today, between Poetry International Archives Iran editor Abol Froushan and Ali Abdolrezaei, a major Iranian poet and leader of a grassroots political movement that has been spreading in Iran since the uprising of January 2018, when the multimedia Colleges of Persian Poetry and of Fiction became a political movement. What incubated as a literary movement calling for democracy of the text and literary styles transformed into a movement for democracy and freedom from the Islamic Republic and its political and economic stranglehold on Iranians – https://bit.ly/2Sn6bPJ
Interview with Helen Knowles by Regine Debatty | Trickle Down, A New Vertical Sovereignty | A prison in Liverpool, an Ethereal Summit in New York city, a prestigious Russian art auction at Sotheby’s, a market in North Manchester. These places and the communities that spend time there have little in common. What is more, they sit at opposite ends of the spectrum of financial power. That’s exactly what appealed to Helen Knowles. Helen Knowles is currently exhibiting the result of this long research at Arebyte Gallery in London – https://bit.ly/2S16mkR
Rowland Atkinson reviews Thomas Piketty’s eagerly awaited new book Capital and ideology in the city | “In all nations and at all times societies require some system or series of defences of the disparities that exist within them. Different kinds of societies have achieved this in their own distinctive ways and in fact much of this more than 1,000 page work delves into the long history of such arrangements. Piketty calls these narratives and systems of thinking inequality regimes. There is power at work in the narratives, ideas and legitimising frameworks deployed by elites and which are shared more broadly within society as a whole.” https://bit.ly/2UtAE1j
OBIETTIVO BOLOGNA REPORTAGE BY ARIANNA FORTE | The itinerant tour of the project DATAPOIESIS runs into Bologna, historically one of the most active and aware Italian cities in urban policies. Datapoiesis in the city, took place from the 24 to 26 of January 2020, coordinated by Singlossa with local partner MaisonVentidue. Obiettivo, was the first datapoietic artwork, and trigger for reflecting on a new kind of processes capable of bringing awareness and social activation using public data in a conscious way and to face complex global phenomena such as poverty from different points of view – https://datapoiesis.com/home/?p=2348
Image from: Data Dating, Exhibition. Wednesday 15 January – Sunday 1 March 2020 at Watermans Art Centre, London.
The FurtherList Archives
https://www.furtherfield.org/the-furtherlist-archives/
For its closing community gathering of the year, the Disruption Network Lab organised a conference to extend and connect its 2019 programme ‘The Art of Exposing Injustice’ – with social and cultural initiatives, fostering direct participation and enhancing engagement around the topics discussed throughout the year. Transparency International Deutschland, Syrian Archive, and Radical Networks are some of the organisations and communities that have taken part on DNL activities and were directly involved in this conference on November the 30th, entitled ‘Activation: Collective Strategies to Expose Injustice’ on anti-corruption, algorithmic discrimination, systems of power, and injustice – a culmination of the meet-up programme that ran parallel to the three conferences of 2019.
The day opened with the talk ‘Untangling Complexity: Working on Anti-Corruption from the International to the Local Level,’ a conversation with Max Heywood, global outreach and advocacy coordinator for Transparency International, and Stephan Ohme, lawyer and financial expert from Transparency International Deutschland.

In the conference ‘Dark Havens: Confronting Hidden Money & Power’ (April 2019) – DNL focused its work on offshore financial systems and global networks of international corruption involving not only secretive tax havens, but also financial institutions, systems of law, governments and corporations. On the occasion, DNL hosted discussions about the Panama Papers and other relevant leaks that exposed hundreds of cases involving tax evasion, through offshore regimes. With the contribution of whistleblowers and people involved in investigations, the panels unearthed how EU institutions turn a blind eye to billions of Euros worth of wealth that disappears, not always out of sight of local tax authorities, and on how – despite, the global outrage caused by investigations and leaks – the practice of billionaires and corporations stashing their cash in tax havens is still very common.
Introducing the talk ‘Untangling Complexity,’ Disruption Network community director Lieke Ploeger asked the two members of Transparency International and its local chapter Transparency International Deutschland to touch base after a year-long cooperation with the Lab, in which they have been substantiating how, in order to expose and defeat corruption, it is necessary to make complexity transparent and simple. With chapters in more than 100 countries and an international secretariat in Berlin, Transparency International works on anti-corruption at an international and local level through a participated global activity, which is the only effective way to untangle the complexity of the hidden mechanisms of international tax evasion and corruption.
Such crimes are very difficult to detect and, as Heywood explained, transparency is too often interpreted as simple availability of documents and information. It requires instead a higher degree of participation since documents and information must be made comprehensible, singularly and in their connections. In many cases, corruption and illegal financial activities are shielded behind technicalities and solid legal bases that make them hard to be uncovered. Within complicated administrative structures, among millions of documents and terabytes of files, an investigator is asked to find evidence of wrongdoings, corruption, or tax evasion. Most of the work is about the capability to put dots together, managing to combine data and metadata to define a hidden structure of power and corruption. Like in a big puzzle, all pieces are connected. But those pieces are often so many, that just a collective effort can allow scrutiny. That is why a law that allows transparency in Berlin, on estate properties and private funds, for example, might be able to help in a case of corruption somewhere else in the world. Exactly like in the financial systems, also in anti-corruption, nothing is just local and the cooperation of more actors is essential to achieve results.

The recent case of the Country-by-Country Reporting shows the situation in Europe. It was an initiative proposed in the ‘Action Plan for Fair and Efficient Corporate Taxation‘ by the European Commission in 2015. It aimed at amending the existing legislation to require multinational companies to publicly disclose their income tax in each EU member state they work in. Not many details are supposed to be disclosed and the proposal is limited only to companies with a turnover of at least €750 million, to know how much profit they generate and how much tax they pay in each of the 28 countries. However, many are still reluctant to agree, especially those favouring the profit-shifting within the EU. Some, including Germany, worry that revealing companies’ tax and profit information publicly will give a competitive advantage to companies outside Europe that don’t have to report such information. Twelve countries voted against the new rules, all member states with low-tax environments helping to shelter the profits of the world’s biggest companies. Luxembourg is one of them. According to the International Monetary Fund – through its 600,000 citizens – the country hosts as much foreign direct investment as the USA, raising the suspicion that most of this flow goes to “empty corporate shells” designed to reduce tax liabilities in other EU countries.
Moreover, in every EU country, there are voices from the industrial establishment against this proposal. In Germany, the Foundation of Family Businesses, which despite its name guarantees the interests of big companies, as Ohme remarked, claims that enterprises are already subject to increasingly stronger social control through the continuously growing number of disclosure requirements. It complains about what is considered the negative consequences of public Country-by-Country Reporting for their businesses, stating that member states should deny their consent as it would considerably damage companies’ competitiveness, and turn the EU into a nanny state. But, apart from the expectations and the lobbying activities of the industrial élite, European citizens want multinational corporations to pay fair taxes on EU soil where the money is generated. The current fiscal regimes increase disparities, allow profit-shifting and bank secrecy. The result is that most of the fiscal burden push against less mobile tax-payers, retirees, employees, and consumers, whilst corporations and billionaires get away with their misconducts.
Transparency International encourages citizens all over the globe to carry on asking for accountability and improvements in their financial and fiscal systems without giving up. In 1997, the German government made bribes paid to foreign officials by German companies tax-deductible, and until February 1999 German companies were allowed to bribe in order to do business across the border, which was common practice, particularly in Asia and Latin America since at least the early 70s. But things have changed. Ohme is aware of the many daily scandals related to corruption and tax evasion: for this reason he considers the work of Transparency International necessary. However, he invited his audience not to describe it as a radical organisation, but as an independent one that operates on the basis of research and objective investigations.
In the last months of 2019 in Germany, the so-called Cum-Ex scandal caught the attention of international news outlets as investigators discovered a trading scheme exploiting a tax loophole on dividend payments within the German tax code. Authorities allege bankers helped investors reap billions of euros in illegitimate tax refunds, as Cum-Ex deals involved a trader borrowing a block of shares to bet against them, and then selling them on to another investor. In the end, parties on both sides of the trade could claim a refund of withholding taxes paid on the dividend, even though prosecutors contend that only a single rebate was actually due. The loophole was closed in 2012, but investigators think that in the meantime companies like Freshfields advised many banks and other participants in the financial markets to illegally profit from it.
As both Heywood and Ohme stressed, we need measures that guarantee open access to relevant information, such as the beneficial owners of assets which are held by entities, and arrangements like shell companies and trusts – that is to say, the info about individuals who ultimately control or profit from a company or estate. Experts indicate that registers of beneficial owners help authorities prosecute criminals, recover stolen assets, and deter new ones; they make it harder to hide connections to illicit flows of capital out of a national budget.
Referring to the case of the last package of measures regarding money laundering and financial transparency, under approval by the German parliament, Ohme showed a shy appreciation for the improvements, as real estate agents, gold merchants, and auction houses will be subject to tighter regulations in the future. Lawmakers complained that the US embassy and Apple tried to quash part of these new rules and that during the parliamentary debate they sought to intervene with the Chancellery to prevent a section of the law from being adopted. The attempt was related to a regulation which forces digital platforms to open their interfaces for payment services and apps, such as the payment platform ApplePay, but it did not land. Apple’s behaviour is a sign of the continuous interferences of the interests at stake when these topics are discussed.
At the end of the first talk, DNL hosted a screening of the documentary ‘Pink Hair Whistleblower’ by Marc Silver. It is an interview with Christopher Wylie, who worked for the British consulting firm Cambridge Analytica, who revealed how it was built as a system that could profile individual US voters in 2014, to target them with personalised political advertisements and influence the results of the elections. At the time, the company was owned by the hedge fund billionaire Robert Mercer and headed by Donald Trump’s key advisor, and architect of a far-right network of political influence, Steve Bannon.
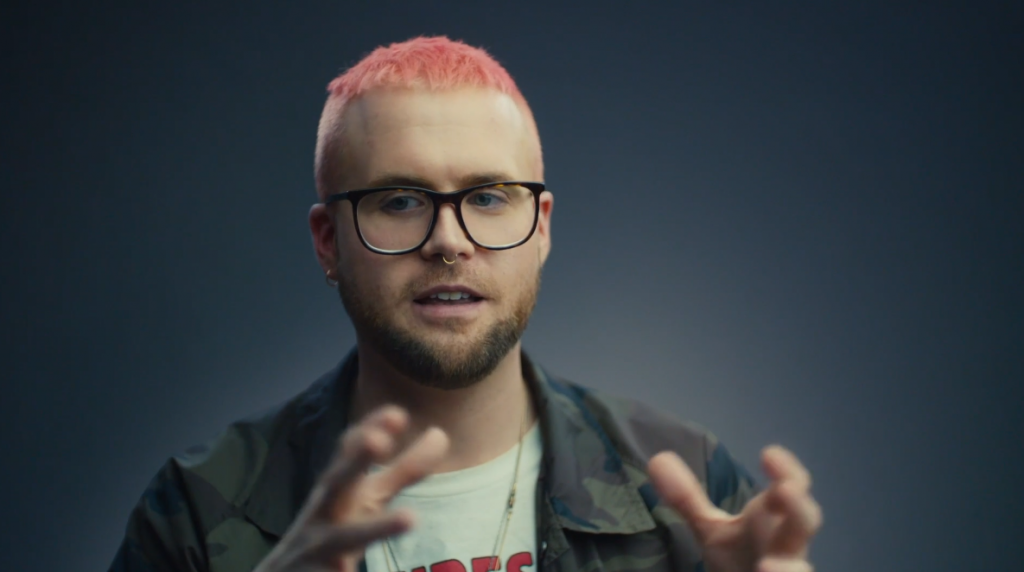
The DNL discussed this subject widely within the conference ‘Hate News: Manipulators, Trolls & Influencers’ (May 2018), trying to define the ways of pervasive, hyper-individualized, corporate-based, and illegal harvesting of personal data – at times developed in partnership with governments – through smartphones, computers, virtual assistants, social media, and online platforms, which could inform almost every aspect of social and political interactions.
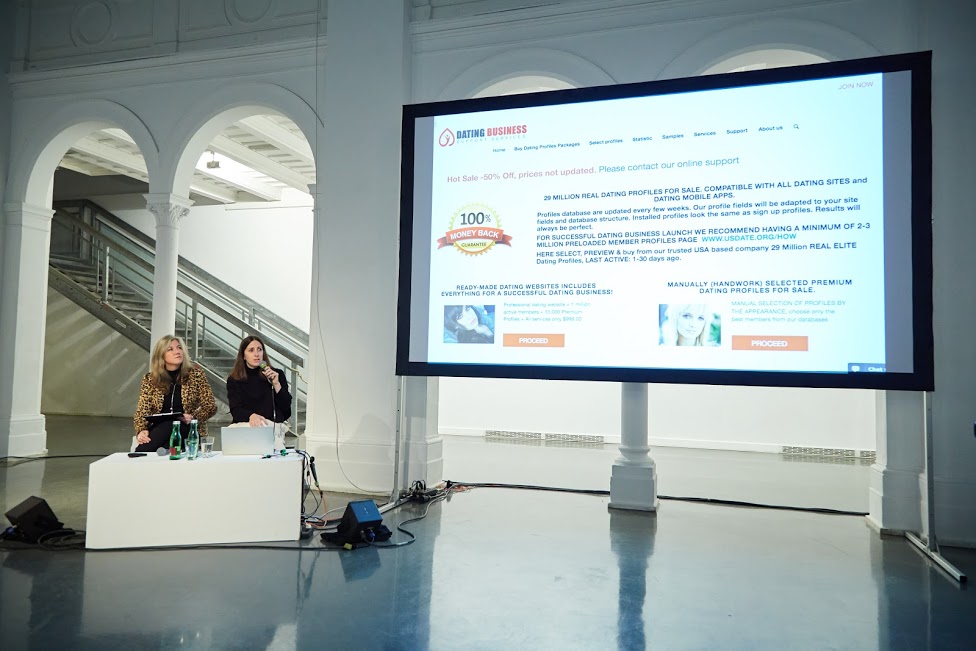
With the overall theme ‘AI Traps: Automating Discrimination‘ (June 2019), DNL sought to define how artificial intelligence and algorithms reinforce prejudices and biases in society. These same issues were raised in the Activation conference, in the talk ‘An Autopsy of Online Love, Labour, Surveillance and Electricity/Energy.’ Joana Moll, artist and researcher, in conversation with DNL founder Tatiana Bazzichelli, presented her latest projects ’The Dating Brokers’ and ‘The Hidden Life of an Amazon User,’ on the hidden side of IT-interface and data harvesting.
The artist’s work moves from the challenges of the so-called networked society to a critique of social and economic practices of exploitation, which focuses on what stands behind the interface of technology and IT services, giving a visual representation of what is hidden. The fact that users do not see what happens behind the online services they use has weakened the ability that individuals and collectives have to define and protect their privacy and self-determination, getting stuck in traps built to get the best out of their conscious or unconscious contribution. Moll explains that, although most people’s daily transactions are carried out through electronic devices, we know very little of the activities that come with and beyond the interface we see and interact with. We do not know how the machine is built, and we are mostly not in control of its activities.
Her project ‘The Dating Brokers’ focuses on the current practices in the global online dating ecosystem, which are crucial to its business model but mostly opaque to its users. In 2017, Moll purchased 1 million online dating profiles from the website USDate, a US company that buys and sells profiles from all over the world. For €136, she obtained almost 5 million pictures, usernames, email addresses, details about gender, age, nationality, and personal information such as sexual orientation, private interests, profession, physical characteristics, and personality. Analysing few profiles and looking for matches online, the artist was able to define a vast network of companies and dating platforms capitalising on private information without the consent of their users. The project is a warning about the dangers of placing blind faith in big companies and raises alarming ethical and legal questions which urgently need to be addressed, as dating profiles contain intimate information on users and the exploitation and misuse of this data can have dramatic effects on their lives.
With the ongoing project ‘The Hidden Life of an Amazon User,’ Moll attempts to define the hidden side of interfaces. The artist documented what happens in the background during a simple order on the platform Amazon. Purchasing the book ‘The Life, Lessons & Rules for Success’ by Amazon founder Jeff Bezos her computer was loaded with so many scripts and requests, that she could trace almost 9,000 pages of lines of code as a result of the order and more than 87 megabytes of data running in the background of the interface. A large part of the scripts are JavaScript files, that can theoretically be employed to collect information, but it is not possible to have any idea of what each of these commands meant.

With this project, Moll describes the hidden aspects of a business model built on the monitoring and profiling of customers that encourages them to share more details, spend more time online, and make more purchases. Amazon and many other companies aggressively exploit their users as a core part of their marketing activity. Whilst buying something, users provide clicks and data for free and guarantee free labour, whose energy costs are not on the companies’ bills. Customers navigate through the user interface, as content and windows constantly load into the browser to enable interactions and record user’s activities. Every single click is tracked and monetized by Amazon, and the company can freely exploit external free resources, making a profit out of them.
The artist warns that these hidden activities of surveillance and profiling are constantly contributing to the release of CO2. This due to fact that a massive amount of energy is required to load the scripts on the users’ machine. Moll followed just the basic steps necessary to get to the end of the online order and buy the book. More clicks could obviously generate much more background activity. A further environmental cost that customers of these platforms cannot decide to stop. This aspect shall be considered for its broader and long term implications too. Scientists predict that by 2025 the information and communications technology sector might use 20 per cent of all the world’s electricity, and consequently cause up to 5.5 per cent of global carbon emissions.
Moll concluded by saying we can hope that more and more individuals will decide to avoid certain online services and live in a more sustainable way. But, trends show how a vast majority of people using these platforms and online services, are harmful, because of their hidden mechanisms, affecting people’s lives, causing environmental and socio-economic consequences. Moll suggested that these topics should be approached at the community level to find political solutions and countermeasures.

The 17th conference of the Disruption Network Lab, ‘Citizens of Evidence’ (September 2019,) was meant to explore the investigative impact of grassroots communities and citizens engaged to expose injustice, corruption, and power asymmetries. Citizen investigations use publicly available data and sources to autonomously verify facts. More and more often ordinary people and journalists work together to provide a counter-narrative to the deliberate disinformation spread by news outlets of political influence, corporations, and dark money think-tanks. In this Activation conference, in a talk moderated by Nada Bakr, the DNL project and community manager, Hadi Al Khatib, founder and Director of ’The Syrian Archive’, and artist and filmmaker Jasmina Metwaly, altogether focused on the role of open archives in the collaborative production of social justice.
The Panel ‘Archives of Evidence: Archives as Collective Memory and Source of Evidence’ opened with Jasmina Metwaly, member of Mosireen, a media activist collective that came together to document and spread images of the Egyptian Revolution of 2011. During and after the revolution, the group produced and published over 250 videos online, focusing on street politics, state violence, and labour rights; reaching millions of viewers on YouTube and other platforms. Mosireen, who in Arabic recalls a pun of the words “Egypt” and “Determination” which could be translated as “we are determined,” has been working since its birth on collective strategies to allow participation and channel the energies and pulses of the 2011 protesters into a constructive discourse necessary to keep on fighting. The Mosireen activists organised street screenings, educational workshops, production facilities, and campaigns to raise awareness on the importance of archives in the collaborative production of social justice.
In January 2011, the wind of the Tunisian Revolution reached Egyptians, who gathered in the streets to overthrow the dictatorial system. In the central Tahrir Square in Cairo, for more than three weeks, people had been occupying public spaces in a determined and peaceful protest to get social and political change in the sense of democracy and human rights enhancement.
For 5 years, since 2013, the collective has put together the platform ‘858: An Archive of Resistance’ – an archive containing 858 hours of video material from 2011, where footage is collected, annotated, and cross-indexed to be consulted. It was released on 16th January 2018, seven years after the Egyptian protests began. The material is time-stamped and published without linear narrative, and it is hosted on Pandora, an open-source tool accessible to everybody.
The documentation gives a vivid representation of the events. There are historical moments recorded at the same time from different perspectives by dozens of different cameras; there are videos of people expressing their hopes and dreams whilst occupying the square or demonstrating; there is footage of human rights violations and video sequences of military attacks on demonstrators.
In the last six years, the narrative about the 2011 Egyptian revolution has been polluted by revisionisms, mostly propaganda for the government and other parties for the purposes of appropriation. In the meantime, Mosireen was working on the original videos from the revolution, conscious of the increasing urgency of such a task. Memory is subversive and can become a tool of resistance, as the archive preserves the voices of those who were on the streets animating those historical days.
Thousands of different points of views united compose a collection of visual evidence that can play a role in preserving a memory of events. The archive is studied inside universities and several videos have been used for research on the types of weapons used by the military and the police. But what is important is that people who took part in the revolution are thankful for its existence. The archive appears as one of the available strategies to preserve people’s own narratives of the revolution and its memories, making it impermeable to manipulations. In those days and in the following months, Egypt’s public spaces were places of political ferment, cultural vitality, and action for citizens and activists. The masses were filled with creativity and rebellion. But that identity is at risk to disappear. That kind of participation and of filming is not possible anymore; public spaces are besieged. The archive cannot be just about preserving and inspiring. The collective is now looking for more videos and is determined to carry on its work of providing a counter-narrative on Egyptian domestic and international affairs, despite tightened surveillance, censorship, and hundreds of websites blocked by the government.

There are many initiatives aiming to resist forgetting facts and silencing independent voices. In 2019, the Disruption Network Lab worked on this with Hadi Al Khatib, founder and director of ‘The Syrian Archive,’ who intervened in this panel within the Activation conference. Since 2011, Al Khatib has been working on collecting, verifying, and investigating citizen-generated data as evidence of human rights violations committed by all sides in the Syrian conflict. The Syrian Archive is an open-source platform that collects, curates, and verifies visual documentation of human rights violations in Syria – preserving data as a digital memory. The archive is a means to establish a verified database of facts and represents a tool to collect evidence and objective information to put an order within the ecosystem of misinformation and the injustices of the Syrian conflict. It also includes a database of metadata information to contextualise videos, audios, pictures, and documents.
Such a project can play a central role in defining responsibilities, violations, and misconducts, and could contribute to eventual post-conflict juridical processes since the archive’s structure and methodology is supposed to meet international standards. The Syrian conflict is a bloody reality involving international actors and interests which is far from being over. International reports in 2019 indicate at least 871 attacks on vital civilian facilities with the deaths of 3,364 civilians, where one in four were children.
The platform makes sure that journalists and lawyers are able to use the verified data for their investigations and criminal case building. The work on the videos is based on meticulous attention to details, and comparisons with official sources and publicly available materials such as photos, footage, and press releases disseminated online.
The Syrian activist and archivist explained that a lot of important documents could be found on external platforms, like YouTube, that censor and erase content using AI under pressures to remove “extremist content,” purging vital human rights evidence. Social media has been recently criticized for acting too slowly when killers live-stream mass shootings, or when they allow extremist propaganda within their platforms.
DNL already focused on the consequences of automated removal, which in 2017 deleted 10 per cent of the archives documenting violence in Syria, as artificial intelligence detects and removes content – but an automated filter can’t tell the difference between ISIS propaganda and a video documenting government atrocities. The Google-owned company has already erased 200,000 videos with documental and historical relevance. In countries at war, the evidence captured on smartphones can provide a path to justice, but AI systems often mark them as inadequate violent content which consequently erases them.
Al Khatib launched a campaign to warn platforms to fix and improve their content moderation systems used to police extremist content, and to consider when they define their measures to fight misinformation and crimes, aspects like the preservation of the common memory on relevant events. Twitter, for example, has just announced a plan to remove accounts which have been inactive for six months or longer. As Al Khatib explains, this could result in a significant loss to the memory of the Syrian conflict and of other war zones, and cause the loss of evidence that could be used in justice and accountability processes. There are users who have died, are detained, or have lost access to their accounts on which they used to share relevant documents and testimonies.
In the last year, the Syrian Archive platform was replicated for Yemen and Sudan to support human rights advocates and citizen journalists in their efforts to document human rights violations, developing new tools to increase the quality of political activism, future prosecutions, human rights reporting and research. In addition to this, the Syrian Archive often organises workshops to present its research and analyses, such as the one in October within the Disruption Network Lab community programme.
The DNL often focuses on how new technologies can advance or restrict human rights, sometimes offering both possibilities at once. For example, free open technologies can significantly enhance freedom of expression by opening up communication options; they can assist vulnerable groups by enabling new ways of documenting and communicating human rights abuses. At the same time, hate speech can be more readily disseminated, technologies for surveillance purposes are employed without appropriate safeguards and impinge unreasonably on the privacy of individuals; infrastructures and online platforms can be controlled to chase and discredit minorities and free speakers. The last panel discussion closing the conference was entitled ‘Algorithmic Bias: AI Traps and Possible Escapes’, moderated by Ruth Catlow, who took the floor to introduce the two speakers and asked them to debate effective ways to define this issue and discuss possible solutions.
Ruth Catlow is co-founder and co-artistic director of Furtherfield, an art gallery in London’s Finsbury Park – home for artworks, labs, and debates based on playful collaborative art research experiences, always across distances and differences. Furtherfield diversifies the people involved in shaping emerging technologies through an arts-led approach, always looking at ways to disrupt network power of technology and culture, to engage with the urgent debates of our time and make these debates accessible, open, and participated. One of its latest projects focused on algorithmic food justice, environmental degradation, and species decline. Exploring how new algorithmic technologies could be used to create a fairer and more sustainable food system, Furtherfield worked on solutions in which culture comes before structures, and human organisation and human needs – or the needs of other living beings and living systems – are at the heart of design for technological systems.
As Catlow recalled, in the conference ‘AI Traps: Automating Discrimination’ (June 2019), the Disruption Network Lab focused on the possible countermeasures to the AI-informed decision-making potential for racial bias and reinforced through AI decision-making tools. It was an inspiring and stimulating event on inclusion, education, and diversity in tech, highlighting how algorithms are not neutral and unbiased. On the contrary, they often reflect, reinforce, and automate the current and historical biases and inequalities of society, such as social, racial, and gender prejudices. The panel within the Activation conference framed these issues in the context of the work by the speakers, Caroline Sinders and Sarah Grant.

Sinders is a machine learning design researcher and artist. In her work, she focuses on the intersections of natural language processing, artificial intelligence, abuse, online harassment, and politics in digital and conversational spaces. She presented her last study on the Intersectional Feminist AI, focusing on labour and automated computer operations.
Quoting Hyman (2017), Sinders argued that the world is going through what some are calling a Second Machine Age, in which the re-organisation of people matters as much as, if not more than, the new machines. Employees receiving a regular wage or salary have begun to disappear, replaced by independent contractors and freelancers; remuneration is calculated on the basis of time worked, output, or piecework, and paid to employees for hours worked. Labour and social rights conquered with hard, bloody fights in the last two centuries seem to be irrelevant. More and more tasks are operated through AI, which plays a big role in the revenues of big corporations. But still, machine abilities are possible just with the fundamental contribution of human work.
Sinders begins her analyses considering that human labour has become hidden inside of automation, but is still integral to that. The training of machines is a process in which human hands touch almost every part of the pipeline, making decisions. However, people who train data models are underpaid and unseen inside of this process. As Thomas Thwaites’ toaster project, a critical design project in which the artist built a commercial toaster from scratch – melting iron and building circuits and creating a new plastic shell – Sinders analyses the Artificial Intelligence economy under the lens of feminist, intersectionalism, to define how and to which extent it is possible to create an AI that respects in all its steps the principles of non-exploitation, non-bias, and non-discrimination.
Her research considers the ‘Mechanical Turks’ model, in which machines masquerade as a fully automated robot but are operated by a human. Mechanical Turk is actually a platform run by Amazon, where people execute computer-like tasks for a few cents, synonymous with low-paid digital piecework. A recent research analysed nearly 4 million tasks on Mechanical Turk performed by almost 3,000 workers found that those workers earned a median wage of about $2 an hour, whilst only 4% of workers on Mechanical Turk earned more than $7,25 an hour. Since 2005 this platform has flourished. Mechanical Turks are used to train AI systems online. Even though it is mostly systematised factory jobs, this labour falls under the gig economy, so that people employed as Mechanical Turks are considered gig workers, who have no paid breaks, holidays, and guaranteed minimum wage.
Sinder concluded that an ethical, equitable, and feminist environment is not achievable within a process based on the competition among slave labourers that discourages unions, pays a few cents per repetitive task and creates nameless and hidden labour. Such a process shall be thoughtful and critical in order to guarantee the basis for equity; it must be open to feedback and interpretation, created for communities and as a reflection of those communities. To create a feminist AI, it is necessary to define labour, data collection, and data training systems, not just by asking how the algorithm was made, but investigating and questioning them from an ethical standpoint, for all steps of the pipeline.

In her talk Grant, founder of Radical Networks, a community event and art festival for critical investigations and creative experiments around networking technology, described the three main planes online users interact with, where injustices and disenfranchisement can occur.
The first one is the control plane, which refers to internet protocols. It is the plumbing, the infrastructure. The protocol is basically a set of rules which governs how two devices communicate with each other. It is not just a technical aspect, because a protocol is a political action which basically involves exerting control over a group of people. It can also mean making decisions for the benefit of a specific group of people, so the question is our protocols but our protocols political.
The Internet Engineering Task Force (IETF) is an open standards organisation, which develops and promotes voluntary Internet standards, in particular, the standards that comprise the Internet protocol suite (TCP/IP). It has no formal membership roster and all participants and managers are volunteers, though their activity within the organisation is often funded by their employers or sponsors. The IETF was initially supported by the US government, and since 1993 has been operating as a standards-development function under the international membership-based non-profit organisation Internet Society. The IETF is controlled by the Internet and Engineering Steering Group (IESG), a body that provides final technical review of the Internet standards and manages the day-to-day activity of the IETF, setting the standards and best practices for how to develop protocols. It receives appeals of the decisions of the working groups and makes the decision to progress documents in the standards track. As Grant explained, many of its members are currently employed for major corporations such as Google, Nokia, Cisco, Mozilla. Though they serve as individuals, this issues a conflict of interests and mines independence and autonomy. The founder of Radical Networks is pessimistic about the capability of for-profit companies to be trusted on these aspects.
The second plane is the user plane, where we find the users’ experience and the interface. Here two aspects come into play: the UX design (user experience design), and the UI (user interface design). UX is the presumed interaction model which defines the process a person will experience when using a product or a website, while the UI is the actual interface, the buttons, and different fields we see online. UX and UI are supposed to serve the end-user, but it is often not like this. The interface is actually optimized for getting users to act online in ways which are not in their best interest; the internet is full of so-called dark patterns designed to mislead or trick users to do things that they might not want.
These dark patterns are part of the weaponised design dominating the web, which wilfully allows for harm of users and is implemented by designers who are not aware of or concerned about the politics of digital infrastructure, often considering their work to be apolitical and just technical. In this sense, they think they can keep design for designers only, shutting out all the other components that constitute society and this is itself a political choice. Moreover, when we consider the relation between technology and aspects like privacy, self-determination, and freedom of expression we need to think of the international human rights framework, which was built to ensure that – as society changes – the fundamental dignity of individuals remain essential. In time, the framework has demonstrated to be plastically adaptable to changing external events and we are now asked to apply the existing standards to address the technological challenges that confront us. However, it is up to individual developers to decide how to implement protocols and software, for example, considering human rights standards by design, and such choices have a political connotation.
The third level is the access plane which is what controls how users actually get online. Here, Grant used Project loon as an example to describe the importance of owning the infrastructure. Project loon by Google is an activity of the Loon LLC, an Alphabet subsidiary working on providing Internet access to rural and remote areas, bringing connectivity and coverage after natural disasters with internet-beaming balloons. As the panellist explained, it is an altruistic gesture for vulnerable populations, but companies like Google and Facebook respond to the logic of profit and we know that controlling the connectivity of large groups of populations provide power and opportunities to make a profit. Corporations with data and profilisation at the core of their business models have come to dominate the markets; many see with suspicion the desire of big companies to provide Internet to those four billions of people that at the moment are not online.
As Catlow warned, we are running the risk that the Internet becomes equal to Facebook and Google. Whilst we need communities able to develop new skills and build infrastructures that are autonomous, like the wireless mesh networks that are designed so that small devices called ‘nodes’ – commonly placed on top of buildings or in windows – can send and receive data and a WIFI signal to one another without an Internet connection. The largest and oldest wireless mesh network is the Athens Wireless Metropolitan Network, or A.W.M.N., in Greece, but we also have other successful examples in Barcelona (Guifi.net) and Berlin (Freifunk Berlin). The goal is not just counterbalancing superpowers of telecommunications and corporations, but building consciousness, participation, and tools of resistance too.

The Activation conference gathered in the Berliner Künstlerhaus Bethanien, the community around the Disruption Network Lab, to share collective approaches and tools for activating social, political, and cultural change. It was a moment to meet collectives and individuals working on alternative ways of intervening in the social dynamics and discover ways to connect networks and activities to disrupt systems of control and injustice. Curated by Lieke Ploeger and Nada Bakr, this conference developed a shared vision grounded firmly in the belief that by embracing participation and supporting the independent work of open platforms as a tool to foster participation, social, economic, cultural, and environmental transparency, citizens around the world have enormous potential to implement justice and political change, to ensure inclusive, more sustainable and equitable societies, and more opportunities for all. To achieve this, it is necessary to strengthen the many existing initiatives within international networks, enlarging the cooperation of collectives and realities engaged on these challenges, to share experiences and good practices.
Information about the 18th Disruption Network Lab Conference, its speakers, and topics are available online:
https://www.disruptionlab.org/activation
To follow the Disruption Network Lab, sign up for its newsletter and get information about conferences, ongoing research, and latest projects. The next event is planned for March 2020.
The Disruption Network Lab is also on Twitter and Facebook.
All images courtesy of Disruption Network Lab
On a blustery cold and wet Sunday in the build up to Christmas I joined a group of people at Furtherfield Commons to discuss the future of Finsbury Park. I finally arrived after prowling around their darkened Gallery in the centre of the park, only to discover the event was being hosted in their other space in the far southeastern corner of the park. This brief detour gave me a moment to breathe in one of my local parks and I experienced a familiar feeling of vulnerability as the night drew in and cold drops of rain started to make themselves felt. The few brave families and exercisers were beginning to retreat as I crossed the open stretch of field that runs parallel to the roaring Seven Sisters Road. Drawn by the welcoming light coming from the building in the small gardens behind the legendary Rowans Ten Pin Bowling and guided by the sound of the drumming, a regular feature of this corner of the park, I entered the workshop and was greeted with mince pies, tea and other goodies, and met the 11 other workshop participants.
Timed to coincide with the 150th anniversary of Finsbury Park, this workshop for local residents, aimed to tap into our experiences and imaginations to generate future visions of the park. The event was led by Dr Rachel Jacobs, who is a local with a special affection for the park, and she started by sharing it’s stories and describing some of the features that are no longer in existence including a bandstand and the many trees that have been removed over the years.
We started by identifying features of the park that we would like to ‘lose’ and those we wanted to ‘protect’. Answers were varied but along similar themes. Many people shared a desire to preserve the trees and if possible, have more. The lake featured prominently with many people wanting to maintain the space and the sanctuary it provides for birds. Rose, one of my fellow workshoppers, gleefully called for those people who feed bread to the ducks to be poisoned.
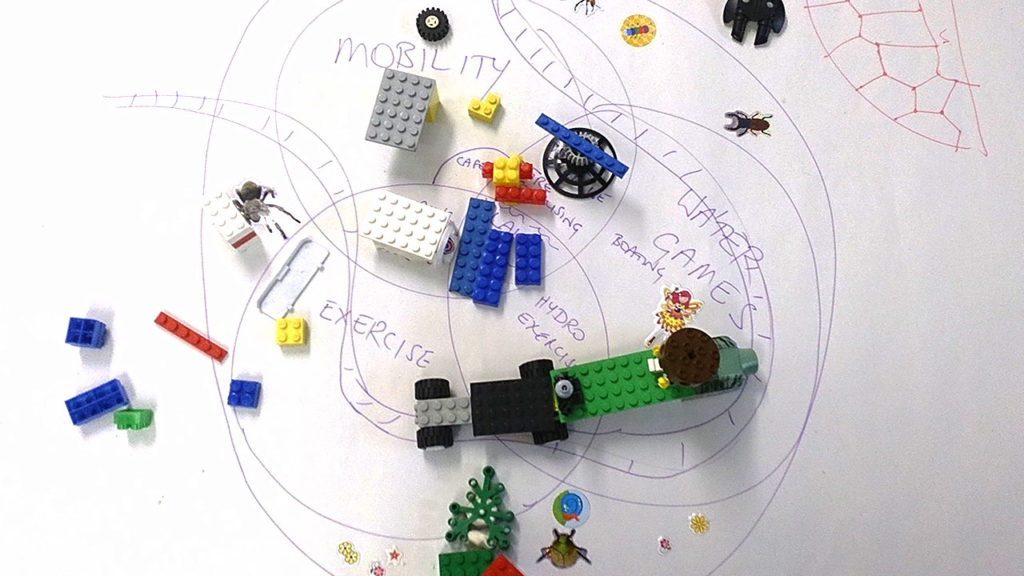
The underground reservoir, a cathedral-like temple to water supply was hailed as a hidden gem that could be utilised as a space during the colder months by Polly a local resident and manager of Space4. Simon, Chair of Friends of Finsbury Park, suggested we consider uses for Manor House Lodge (another building that had escaped my attention). Zeki prioritised the the rocks in the park for protection – especially at the amphitheatre space beside the play park. There were wistful expressions of personal connections to conkers, squirrels and swans. The things that people wanted to lose were more elusive: the atmosphere that the park creates at night; its association with crime and a lack of safety. Gab who overlooks the park from his 8th floor flat, feels the park can be scary and in his words, sometimes ‘sly’. Removing the fences was suggested as a possible remedy.
Next, we were introduced to an initially bemusing process based on Play Your Place, designed by artists Ruth Catlow and Mary Flanagan, to introduce playful and game-like activities to public consultation. We were each asked to select different cards with random words that we were told would help us to disrupt our conventional view of problem solving. The cards were divided into provocative statements, for example mine were: ‘London is no longer’ and ‘getaway car’. Then a spinning wheel contained words associated with game features, like ‘mission’, ‘protagonist’, ‘goal’ or ‘reward’. After drawing or writing out our scenarios based on the random words we had to pick a segment of the wheel in which to place our ideas.

I asked if London is no longer, why is that so? Perhaps the park has eaten London. I was making the park the protagonist, the hero of the story. My ‘getaway car’ card prompted me to imagine Finsbury Park criss-crossed by many roads. So what if a part of the park could move very slowly, a moving park that people could take in the rest of the park from and jump on and off.
Zeki, one of the youngest participants had the cards ‘maps‘ and ‘someone caring for the park’ they assigned it the wheel word ‘reward’. He imagined the rocks in the park could become an area where people could come and paint and draw on the rocks. People will be able to look at the drawings and climb on the rocks. He said this suited ‘reward’ because you get a nice place.
Finally we worked with lego and plasticine, felt and coloured paper, to make a representation of our scenarios. Time flew by before we were then asked to talk about what we had created.
Simon and Talal ended up using a lot of lego. They said they weren’t that confident ‘creating’ but their riotous explosion of lego pieces described the Finsbury Park Lodge with lots of tropical trees growing around them. They included a clocktower which they felt the park needed. Ominously on the edge of their diorama there was, in their words: ‘the threat of a forest fire’.
Ilenia and Gab created intricate visions of the park modelled from tiny pieces of plasticine. Ilenia created crosses to represent all the buildings that she was going to destroy. She said “All the fences will be replaced by nice trees. The lake will be larger than it is now. There will be more people using the park.” Gab described the a tree as becoming “a colourful multi-form creator. It will be very friendly and very different from normal. Everything will be very colourful and this will be linked to representing climate change.” Emma who earlier in the workshop explained her love of conkers ended up building robot conkers.
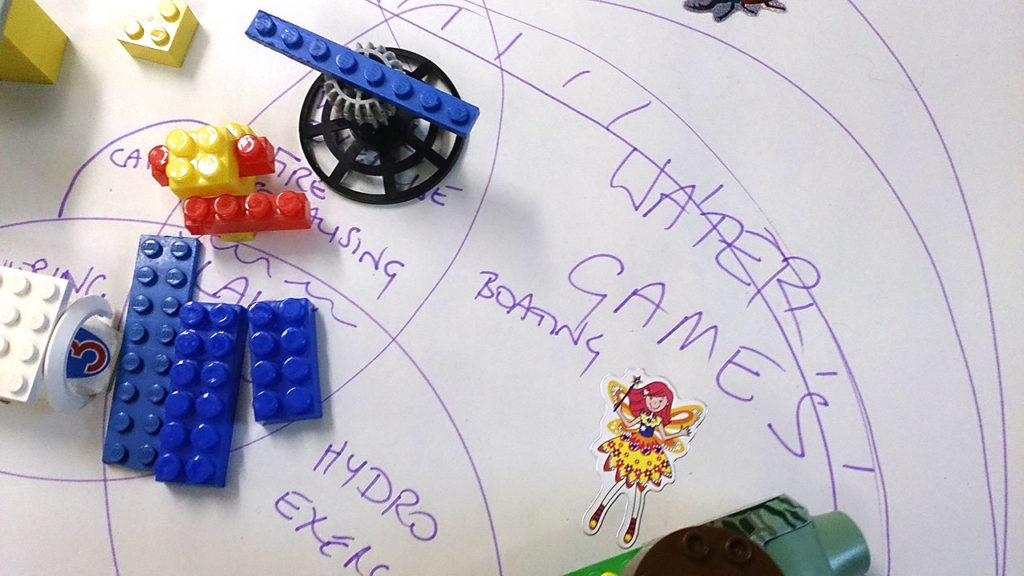
The outcomes were unexpected and realised in a wonderfully ad hoc way with a rich mix of ideas. Rachel and the Furtherfield team were on hand to support and provide more insight. Although the process of drawing cards and selecting from a wheel was initially quite perplexing, staying with the uncertainty of the process meant that we came up with ideas that were novel and unhindered by more formal or conservative notions of preserving or enhancing Finsbury Park. The two hour time limit, meant that everything moved along at pace that kept the idea generation restless. I believe I speak for all who took part in anticipating the results of the wider project.
What can possibly be made from such a kaleidoscope of raw material, I wondered on my way home in the pouring rain? Perhaps my plant car or Emma’s robot conkers will see the light of day or the darkness of the underground reservoir.
Futurescapes is an Innovate UK Audience of the Future Design Foundations project that uses Finsbury Park as a test case to examine the commercial potential for using immersive experiences as a tool for collaborative placemaking for public spaces and integrated public services. Furturescapes is a partnership project with Furtherfield, The Audience Agency and Wolf in Motion.
In thinking about the relationship between science fiction and social justice, a useful starting-point is the novel that many regard as the Ur-source for the genre: Mary Shelley’s Frankenstein (1818). When Shelley’s anti-hero finally encounters his creation, the Creature admonishes Frankenstein for his abdication of responsibility:
I am thy creature, and I will be even mild and docile to my natural lord and king, if thou wilt also perform thy part, the which thou owest me. … I ought to be thy Adam, but I am rather the fallen angel, who thou drivest from joy for no misdeed. … I was benevolent and good; misery made me a fiend. Make me happy, and I shall again be virtuous.
Popularly misunderstood as a cautionary warning against playing God (a notion that Shelley only introduced in the preface to the 1831 edition), Frankenstein’s meaning is really captured in this passage. Shelley, influenced by the radical ideas of her parents, William Godwin and Mary Wollstonecraft, makes it clear that the Creature was born good and that his evil was the product only of his mistreatment. Echoing the social contract of Jean-Jacques Rousseau, the Creature insists that he will do good again if Frankenstein, for his part, does the same. Social justice for the unfortunate, the misshapen and the abused is what underlies the radicalism of Shelley’s novel. Frankenstein’s experiments give birth not only to a new species but also to a new concept of social responsibility, in which those with power are behoved to acknowledge, respect and support those without; a relationship that Frankenstein literally runs away from.
The theme of social justice, then, is there at the birth also of the sf genre. It looks backwards to the utopian tradition from Plato and Thomas More to the progressive movements that characterised Shelley’s Romantic age. And it looks forwards to how science fiction – as we would recognise it today – has imagined future and non-terrestial societies with all manner of different social, political and sexual arrangements.
Shelley’s motif of creator and created is one way of examining how modern sf has dramatized competing notions of social justice. Isaac Asimov’s I, Robot (1950) and, even more so, The Caves of Steel (1954) ask not only the question, ‘can a robot pass for human?’, but also more importantly, ‘what happens to humanity when robots supersede them?’. Within current anxieties surrounding AI, Asimov’s stories are experiencing a revival of interest. One possible solution to the latter question is the policing of the boundaries between human and machine. This grey area is explored through use of the Voigt-Kampff Test, which measures the subject’s empathetic understanding, in Philip K. Dick’s Do Androids Dream of Electric Sheep? (1968) and memorably dramatized in Ridley Scott’s film version, Blade Runner (1982). In William Gibson’s novel, Neuromancer (1984), and the Japanese anime Ghost in the Shell (1995), branches of both the military and the police are marshalled to prevent AIs gaining the equivalent of human consciousness.
Running parallel with Asimov’s robot stories, Cordwainer Smith published the tales that comprised ‘the Instrumentality of Mankind’, collected posthumously as The Rediscovery of Man (1993). A key element involves the Underpeople, genetically modified animals who serve the needs of their seemingly godlike masters, and whose journey towards emancipation is conveyed through the stories. It is surely no coincidence that both Asimov and Smith were writing against the backdrop of the Civil Rights Movement, but it is also indicative of the magazine culture of the period that both had to write allegorically. In N.K. Jemisin’s Broken Earth trilogy (2015-7), an unprecedented winner of three successive Hugo Awards, the racial subtext to the struggle between ‘normals’ and post-humans is made explicit.
Jemisin, like Ann Leckie’s multiple award-winning Ancillary Justice (2013), is indebted to the black and female authors who came before her. In particular, the influence of Octavia Butler, as indicated by the anthology of new writing, Octavia’s Brood (2015), has grown immeasurably since her premature death in 2006. Butler’s abiding preoccupation was with the compromises that the powerless would have to make with the powerful simply in order to survive. Her final sf novels, Parable of the Talents (1993) and Parable of the Sower (1998), tentatively posit a more utopian vision. This hard-won prospect owes something to both Joanna Russ’s no-nonsense ideal of Whileaway in The Female Man (1975) as well as the ‘ambiguous utopia’ of Ursula Le Guin’s The Dispossessed (1974). Leckie, in particular, has acknowledged her debt to Le Guin, but whilst most attention has been paid to the representation of non-binary sexualities in both the Ancillary novels and Le Guin’s The Left Hand of Darkness (1969), what binds both authors is their anarchic sense of individualism and communitarianism.
Whilst sf has, like many of its recent award-winning recipients, diversified over the decades, there is little sense of it having abandoned the Creature’s plaintive plea in Frankenstein: ‘I am malicious because I am miserable.’ It is the imaginative reiteration of this plea that makes sf into a viable form for speculating upon the future bases of citizenship and social justice.
We are delighted to share with you our Spring season of art and blockchain essays, interviews and events, offering a wide spread of exploration and critique.
The blockchain is an evocative concept, but progress in ideas of cryptographic decentralisation didn’t stop in 2008. It’s helpful for artists to get a sense of the plasticity of new technical media. So first we are pleased to share with you Blockchain Geometries a guide by Rhea Myers to the proliferation of blockchain forms, ideas and their practical and imaginative implications.
In Moods of Identification Emily Rosamond writes her response to our second DAOWO workshop, Identity Trouble (on the blockchain). She reflects on both ongoing attempts to reliably verify identity, and continuing counter-efforts to evade such verifications.
Mat Dryhurst and Holly Herndon speak here with Marc Garrett in an interview republished from our book with Torque Editions Artists Re:Thinking the Blockchain (2017). Mat and Holly convey a sense of excitement about developments and opportunities for new forms of decentralised collaboration in music.
Finally you can book your place on future events at the DAOWO blockchain laboratory and debate series for reinventing the arts.[note] DAOWO is inspired by a paper written by artist, hacker and writer Rhea Myers called DAOWO – Decentralised Autonomous Organisation With Others.[/note] Download the DAOWO Resource #1 for key learnings, summaries of presentations, quotes, photographs, visualisations, stories and links to videos, audio recordings and much more from our first two events about developments in the arts and the trouble with Identity.
The blockchain is 10 years old and is surrounded with a hype hardly seen since the arrival of the Web. We’d like to see more variety in the imaginaries that underpin blockchains and the backgrounds of the people involved because technologies develop to reflect the values, outlooks and interests of those that build them.
Artists have worked with digital communication infrastructures for as long as they have been in existence, consciously crafting particular social relations with their platforms or artwares. They are also now widely at work in the creation of blockchain-native critical artworks like Clickmine by Sarah Friend[note]The 2017 Furtherfield and NEoN commission as part of the State Machines EU cooperation programme[/note] and Breath (BRH) by Max Dovey, Julian Oliver’s cryptocurrency climate-change artwork, Harvest (see featured image) and 2CE6… by Lars Holdhus[note]Featured as part of Øx, an exhibition of cryptographic artwork curated by Sam Hart as part of the Ethereal Summit, NYC. 2017[/note], to name but a few.

By making connections that need not be either utilitarian nor profitable, artists explore potential for diverse human interest and experience. Also, unlike on blockchains, where time moves inexorably forward (and only forward) – fixing the record of every transaction made by its users, into its time slot, in a steady pulse, one block at a time – human imaginative curiosity can scoot, meander and cycle through time, inventing and testing, intuiting and conjuring, possible scenarios and complex future worlds. They allow us to inhabit, in our imaginations, new paradigms without unleashing actual untested havoc upon our bodies and societies.

Back in 2008 the global banking system was bailed out by governments with tax payers’ money. Meanwhile a 15 year explosion of web-inspired, decentralised, mutualist-anarchist DIWO (Do It With Others)-style cultural actions and practices ebbed (though its roots remain and go deep). The global network of human attention and resources were, by this time, well and truly re-centralised. The “big five” now owned, and often determined, our communication and expression. Post-Internet artists rejected platform-building as a social artform and instead, took as their materials, lives mediated through social media and corporate owned platforms. Some dived into the marketing vortex, to revel and participate in the heightened commodification of art.
With the introduction of the blockchain protocol on the Internet we see a reversed direction of travel in the artworld, with major developments coming more quickly from the businesses of art, which reassert art’s primary status as an asset class, than from those artists experimenting with new forms of experience and expression enabled by its affordances. Now intermediaries of art world business are moving into blockchains (also sometimes called the “Internet of money”) with a focus on provenance, authentication, digital arts made scarce again with IP tracking, fractional ownership, securitisation and auction[note]See the Blockchain Art Stack Ready Reckoner, DAOWO Resource #1, page 19[/note]. It is blockchains for art, any art, as long as that art can be owned and commodified. This may be seen as a good thing, generating and distributing increased revenues to ‘starving artists’. Also perhaps inevitable, as that which cannot be owned is hard to represent on a blockchain ledger.
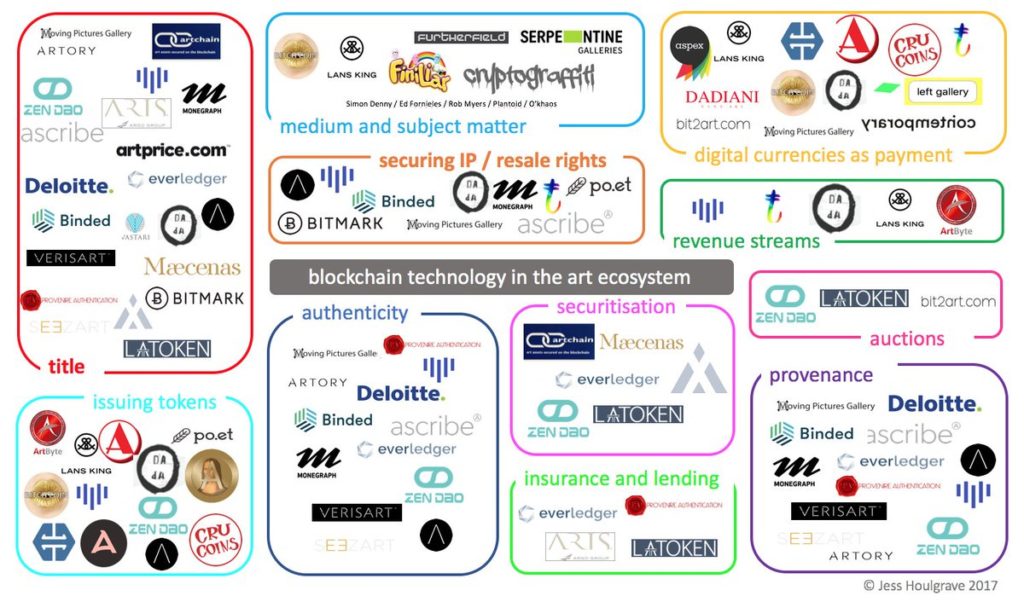
In his new book Reinventing democracy for the digital condition, (2018) Felix Stalder notes that people are increasingly actively (voluntarily and/or compulsorily) participating in the negotiation of social meaning through the “referentiality, communality, and algorithmicity, […] characteristic cultural forms of the digital condition”. In 2015 the Ethereum blockchain launched with a new layer that could run “smart contracts”, pieces of code which act as autonomous agents, performing the function of a legal agreement without the interference of a corruptible or fallible human[note]These technologies now underpin a range of post-currency developments, massive industrial and state investment for authentication of identity and matter, more efficient and secure financial transactions and distribution of digital assets; communications so secure as to facilitate voting; and as a coordinating technology for the billions of devices connected to the Internet.[/note]. These can be combined to perform as blockchain-based companies called Distributed Autonomous Organizations (DAOs) and there are a plethora of blockchain implementations and political agendas now developing. How these unfurl will affect our ability to relate to each other, to deliberate, decide and cooperate with each other as individuals, organisations and societies.
So for us the promise lies in platform-building: by-and-for communities of experimental artists (in the expanded sense of the word), participants and audiences who want to create not just saleable or tradeable art objects[note]For examples like Cryptopunks, Cryptokitties and Rare Pepes read Tokenization and its Discontents by Rhea Myers, Furtherfield 2017[/note] but artworks that critique the relationship between art and money, and expand the contexts in which art is made and valued.
‘AltCoins, cryptotokens, smart contracts and DAOs [Digital Autonomous Organisations] are tools that artists can use to explore new ways of social organisation and artistic production. The ideology and technology of the blockchain and the materials of art history (especially the history of conceptual art) can provide useful resources for mutual experiment and critique’ – Rhea Myers[note](Conceptual) Art, Cryptocurrency and Beyond by Rhea Myers, Furtherfield 2014[/note]
While FairCoin (being rolled out by FairCoop with the Catalan Integral Cooperative) puts new forms of decentralised social organisation into practice on the ground, blockchain based art projects such as Terra0 and Plantoid by O’khaos offer examples of governance systems and invite us to critically “imagine a world in which responsibility for many aspects of life (reproduction, decision-making, organisation, nurture, stewardship) are mechanised and automated.”[note]Both featured in the exhibition NEW WORLD ORDER, currently touring as part of the State Machines programme to Aksioma in Slovenia and Drugo More in Croatia[/note] Both artworks demonstrate functioning systems and help us to think through how we might determine and distribute artistic (and other) resources, their value, and the rules for their co-governance for the kinds of freedoms, commonalities and affiliations that are important for the arts.

It may take a while. What to value and how to value it is a particularly tangled question. The technical infrastructure of the blockchain is at the stage of development that the Web was at in the early 90s (blockchain technologies are less forgiving, require deeper programming knowledge and are therefore more expensive to build than web pages or platforms) which, along with the get-rich-quick vibe of non-community-platform projects, might be why there are still so few community platforms actually in operation. Resonate.is the cooperatively owned music streaming service is an inspiration in this regard. It is a platform for musicians – creators and listeners – that opens up the governance of its resources to everyone who has ever created or listened to its music. It demonstrates one way in which a DIWO ethos might work.
Helen Kaplinsky is exploring how to bootstrap to the blockchain, Maurice Carlin’s Temporary Custodians project which realises an alternative system of peer2peer art ownership and stewardship at Islington Mill[note]See An Alternative to a Historical Mode of Art Ownership, Helen Kaplinsky in DAOWO Resource #1, page 6, Furtherfield, 2018[/note].
Three preoccupations dominate 2018 New Year blogs and commentary that mark the blockchain’s 10th anniversary: blockchains as cash cults; doubts about the actual utility of blockchains and; the environmental impact of Bitcoin (still, erroneously interchangeable with the blockchain in the minds of lots of people). We add to these our concern about the intensification of control enabled by these infrastructures, AND the simultaneous conviction (shaped by deep collaborations and hard criticisms over the last years) that blockchains have the potential to enable and stimulate new forms of social organisation, resource distribution and collaboration in the arts.
The first two preoccupations match exactly the commentary surrounding the early days of the Web and we know how that turned out. The remaining concerns are grist to the mill of our ongoing programme of publications, films, exhibitions and events. The technologies are only now stabilising to allow more grass-roots infrastructural developments.
We invite you to bring your own lens of constructive critique, gather a crowd to debate and explore how we might pull blockchains into art, on the arts’ own terms, and to gain an understanding of why it is worthwhile.
If you’re interested in Furtherfields critical art and blockchain programmes with various individuals, groups and partners since 2015. You could check out how it all started, watch our short film, read this book, visit this exhibition, or archives and documents of previous exhibitions[note]The Human Face of Cryptoeconomies[/note], [note]New World Order[/note], read reviews and debate, and join us at our ongoing DAOWO blockchain lab series, devised with Ben Vickers (Serpentine Galleries) in collaboration with the Goethe-Institut London, and the State Machines programme[note] Its title is inspired by a paper written by artist, hacker and writer Rhea Myers called DAOWO – Decentralised Autonomous Organisation With Others.[/note]
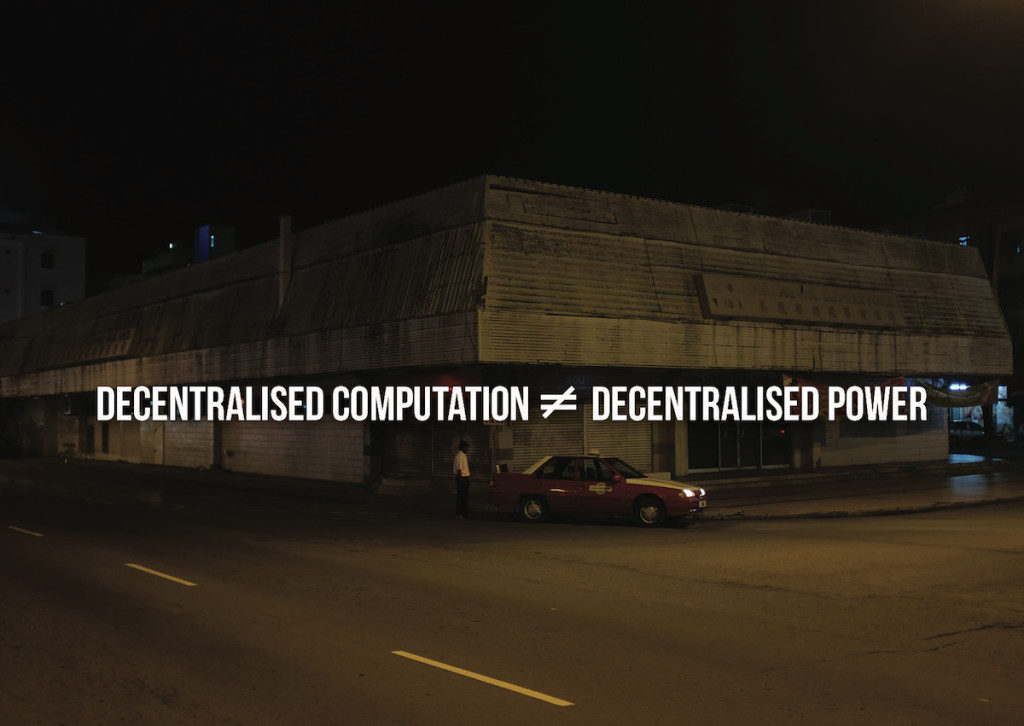
This essay is a response to Identity Trouble (on the blockchain), the second in the DAOWO lab series for blockchain and the arts. Rosamond reflects on both ongoing attempts to reliably verify identity, and continuing counter-efforts to evade such verifications.
Online transactions take place in a strange space: one that blurs the distinctions between the immediate and the remote, the intimate and the abstract. Credit card numbers, passing from fingers to keyboards to Amazon payment pages, manage complex relations between personal identity and financial capital that have been shifting for centuries. Flirtations on online dating platforms – loosely tied to embodied selves with a pic or two and a profile – constitute zones of indistinction between the intimate spheres of the super-personal, and hyper-distributed transnational circuits of surveillance-capital. Twitter-bot invectives mix with human tweets, swapping styles – while all the while bot-sniffing Twitter bots try to distinguish the “real” from the “fake” voices[1]. Questions of verification – Who is speaking? Who transacts? – proliferate in such spaces, take on a new shape and a shifted urgency.
How does personal identity interface with the complex and ever-changing technical infrastructures of verification? How is it possible to capture the texture of “identity trouble” in online contexts today? The second in the DAOWO event series, “Identity Trouble (on the blockchain),” addressed these questions, bringing together a range of artists, developers and theorists to address the problems and potentials of identification, using technical apparatuses ranging from blockchain, to online metrics, to ID cards and legal name changes. The day included reflections on both ongoing attempts to reliably verify identity, and continuing counter-efforts to evade such verifications.
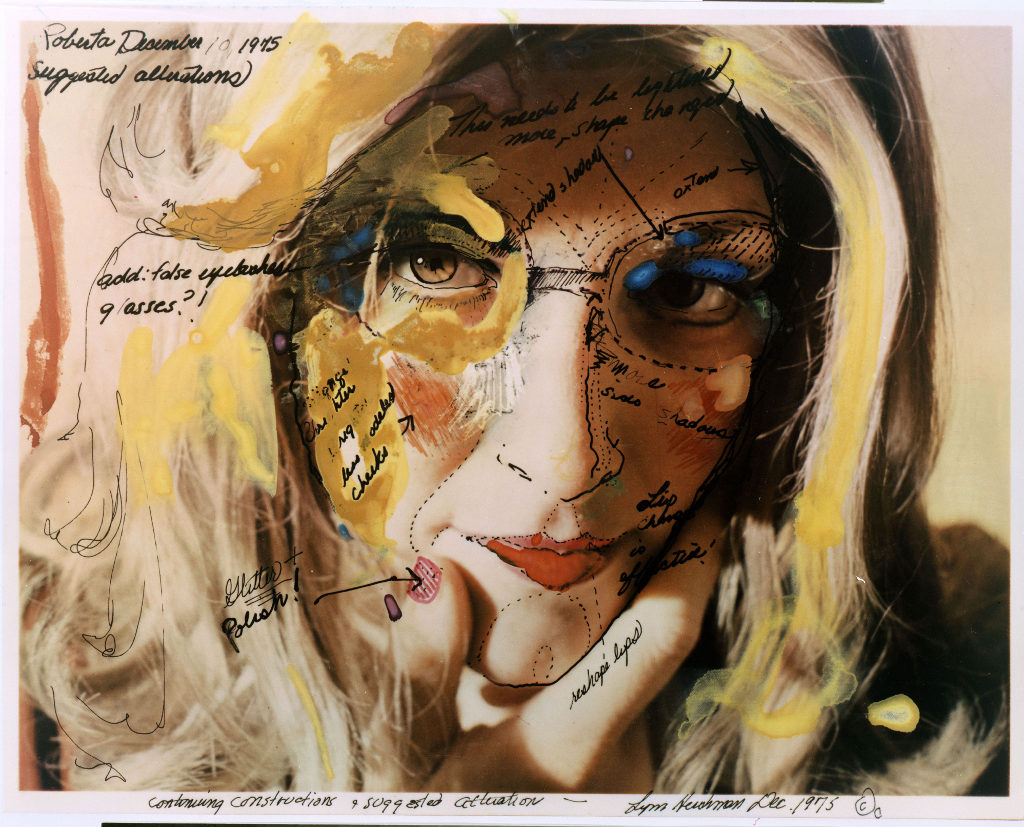
Before going into the day in any detail (and at the risk of going over some already well-trodden ground), I want to try to piece together something which might – however partially – address the deeper histories of the problems we discussed. Of course, identity was an elusive concept long before the internet; and the philosophical search to understand it has run parallel to a slow evolution in the technical and semiotic procedures involved in its verification. In fact, seen from one angle, the period from the late nineteenth century to present can be understood as one in which an increasing drive to identify subjects (using photo ID cards, fingerprints, signatures, credit scores, passwords, and, now, algorithmic/psychometric analysis based on remote analysis of IP address activity) has been coupled with a deep questioning of the very concept of identity itself.
On the one hand, as John Tagg describes, in the second half of the nineteenth century, the restructuring of the nation-state and its disciplinary institutions (“police, prisons, asylums, hospitals, departments of public health, schools and even the modern factory system itself”[2]), depended on creating new procedures for identifying people. This involved, among other things, yoking photography to the evidentiary needs of the state – for instance, through Alphonse Bertillon’s anthropometric identity card system, invented in 1879 and adopted by French police in the 1880s. The identity cards, filed by police, included suspects’ photographs and measurements, and helped them spot repeat offenders.
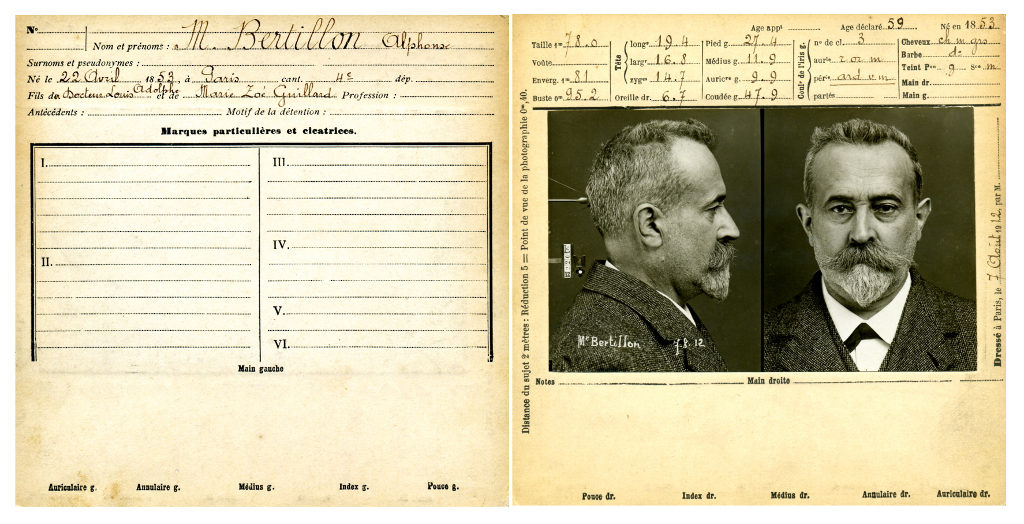
This impulse to identify, it seems, has only expanded in recent times, given the proliferation of biometric and psychometric techniques designed to pin down persons. On the biometric end of this spectrum, retinal scans, biometric residence permits and gait recognition technologies manage people’s varying levels of freedom of movement, based on relatively immutable bodily identifiers (the retina; the photographic likeness; the fingerprint; the minute particularities of the gait). On the psychometric end of the spectrum, private companies calculate highly speculative characteristics in their customers by analysing their habits – such as “pain points.” The American casino chain Harrah’s, for instance, pioneered in analysing data from loyalty cards in real time, to calculate the hypothetical amount of losses a particular gambler would need to incur in order to leave the casino. The pain point – a hypothetical amount of losses calculated by the company, which may be unknown to the customer herself – then provided the basis for Harrah’s’ real-time micro-management of customer emotion, enabling them to send “luck ambassadors” out onto the floor in real time to boost the spirits of those who had a bad day [3].
On the one hand, then, identification apparatuses have become ever more pervasively intertwined with the practices of daily life in industrialized societies since the latter half of the nineteenth century; this produced new forms of inclusion and exclusion of “exceptional” subjects within various institutional regimes. On the other hand, just as the technical and semiotic procedures associated with verifying identity were proliferating and becoming ever harder to evade, modern and postmodern thinkers were deeply questioning what, exactly, could possibly be identified by such procedures – and why identity had become such a prominent limiting condition in disciplinary societies. James Joyce’s character Stephen Dedalus marvels at the lack of cellular consistency in the body over a lifetime. While an identifying trait, such as a mole on the right breast, persists, the cells of which it is made regenerate repeatedly. (“Five months. Molecules all change. I am other I now.” [4]) How, then, can debts and deeds persist, if the identificatory traits to which they are indexed are intangibly inscribed in an ever-changing substrate of cellular material?
In the mid-twentieth century, Foucault and Barthes deeply questioned the limitations identity imposed on reading and interpretation. Why, for instance, need authorship play such a prominent role in limiting the possible interpretations of a text? “What difference does it make who is speaking?” [5]
In ’nineties identity discourse, theories of difference became particularly pronounced. Cultural theorists such as Stuart Hall radically questioned essentialist notions of cultural identity, while nonetheless acknowledging the political and discursive efficacy of how identities come to be narrated and understood. Hall and others advocated for a critical understanding of identity that emphasized “not ‘who we are’ or ‘where we came from’, so much as what we might become, how we have been represented and how that bears on how we might represent ourselves. Identities are… constituted within, not outside representation.” [6]
On the one hand – so I have said – myriad technical apparatuses have aimed to ever more reliably capture and verify identity. On the other hand, myriad critical texts have questioned identity’s essentialist underpinnings. But today, these lines have become blurred. The anti-identitarian mood permeates technical landscapes, too – not just theoretical ones. Fake IDs, identity theft, and other obfuscations have grown ever more complex alongside apparatuses for identification; indeed, such fakeries have both emerged in response to, and driven yet further developments in technologies for identity verification as is the case in a Fully-Verified system. The frontiers of identification are ever-changing; each attempt to improve technologies for verifying identity, it seems, eventually provokes the invention of new techniques for evading those verifications.
At the inherently uncertain point of contact between person and online platform, new forms of anti-identifications are practiced – invented or adapted from previous stories. In one bizarre example from 2008, a Craigslist advert posted in Monroe, Washington requested 15-20 men for a bit of well-paid maintenance work. The men were to turn up at 11:15 am in front of the Bank of America, wearing dark blue shirts, a yellow vest, safety goggles and surgical masks. As it turned out, there was no work to be had; instead, the men had been summoned to acts as decoys for a robbery – a squid-ink trail of similarity to help the thief escape. The idea, though inventive, wasn’t entirely original; it was described by police as a possible copycat of the plot in the film The Thomas Crown Affair (1999) [7.
Today, the anti-identitarian mood has spread far beyond small-scale manoeuvers like this. Multiple large-scale data breaches – such as the recent Equifax breach, which compromised the data of over 145 million customers [8] – have put a cloud over the veracity of millions of people’s online identities. The anti-identitarian mood becomes broad, pervasive, and generalized in data-rich, security-compromised environments. It becomes a kind of weather – a storm of mistrust that gathers and subsides on the level of infrastructures and populations.
Such are some of the complexities that the DAOWO speakers had to contend with. At the Goethe Institute, we thought through some of the ways in which identities are being newly constituted within representation – ways that might, indeed, answer to the technical and philosophical problems associated with identification. Backend developer Thor Karlsson led us through his company Authenteq’s quest to provide more reliable online identity verification. Citing the ease with which online credit card transactions can be hacked, and with which fake accounts proliferate, Karlsson described Authenteq’s improved ID verification process – a digital biometric passport, using blockchain as its technical basis. Users upload a selfie, which is then analysed to ensure that it is a live image – not a photograph of a photograph, for instance. They also upload their passport. Authenteq record their verification, and return proof of identity to users, on the BigChainDB blockchain.
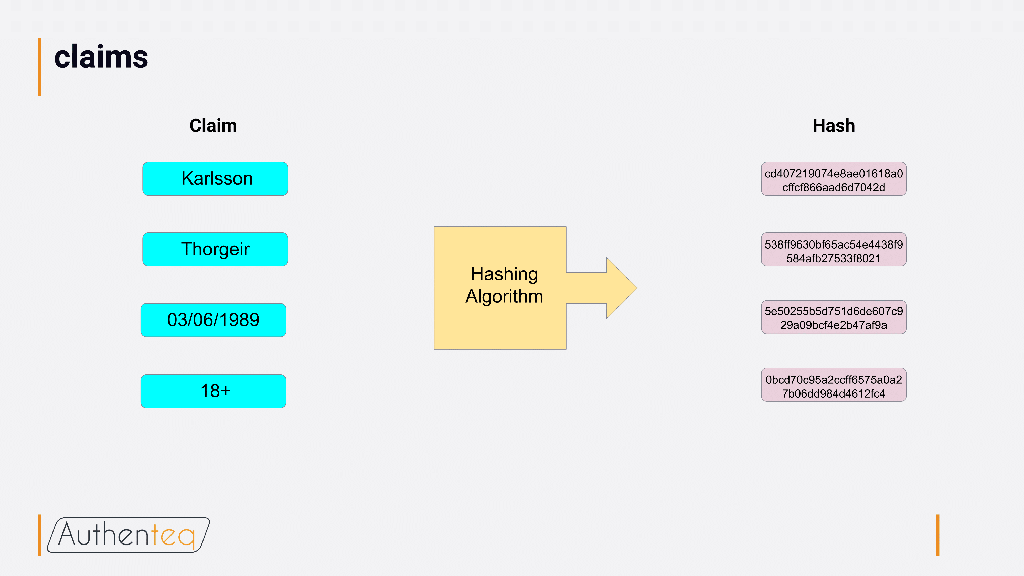
A hashing algorithm ensures that users can be reliably identified, without a company having to store any personal information about them. Authenteq aims to support both identity claim verifications and KYC (Know Your Customer) implementations, allowing sites to get the information they need about their users (for instance, that they are over 18 for adults-only sites) without collecting or storing any other information about them. Given how much the spate of recent large-scale data breaches has brought the storage of personal data into question, Authenteq’s use of blockchain to circumvent the need to store personal data promises a more secure route to verification without revealing too much of personal identity.
Nonetheless, while Karlsson and Authenteq were optimistic that they can make meaningful improvements in online identification processes, other provocations focused on the potential problems associated with such attempts at identification – on the protological level, on the level of valuation, and on the level of behaviour-as-protocol. Ramon Amaro delivered an insightful critique of blockchain and the problem of protological control. There is no such thing as raw data – inputs are always inflected by social processes. Further, the blockchain protocol relies heavily on consensus (with more focus on consensus than on what, exactly, is being agreed upon) – which reflects a need to protect assets (including identity) and oust enemies that is, ultimately, a capitalist one. Given this, how can identity manoeuver within the blockchain protocol, without always already being part of a system that is based on producing inclusions and exclusions – drawing lines between those who can and cannot participate?
My own contribution focused on systemic uncertainty in the spheres of personal valuation, looking at online reputation. In a world in which online rankings and ratings pervade, it seems that there is a positivist drive to quantify online users’ reputations. Yet such apparent certainty can have unexpected effects, producing overall systemic volatility. At the forefront of what I call “reputation warfare,” strategists such as Steve Bannon invent new ways to see systemic reputational volatility as a source of value itself, producing options for the politicians they represent to capitalize on the reputational violence produced on sites like 4chan and 8chan.
While these contributions reflected on some of the critical problems associated with pinning down identity’s value, some of the artists’ contributions for the day focused on the ludic aspects of identity play. Ed Fornieles’ contribution focused on the importance of role play as a practice of assuming alternate identities. In his work, this involves thinking of identity as systemic, not individual – and considering how it might be hacked. In many of Fornieles’ works, this involves focusing attention on the relation between identity and the platforms on which they are played out. Behaviour becomes a kind of protocol; role play becomes a reflection on strands of behaviour as protocol.

We ended the day with a screening and discussion of My Name is Janez Janša (2012), a film by three artists who, in 2007, collectively changed their names to Janez Janša, to match that of the current president of Slovenia. The film, an extended meditation on the erosion of the proper name as an identifier, catalogued many instances of ambiguity in proper names – from the unintended (an area of Venice in which huge numbers of families share the same last name) to the intentional (Vaginal Davis on the power of changing names). It also charted reactions to the three artists’ act of changing their name to Janez Janša. What seemed to confound people was not so much that their names had been changed, but rather that the intention of the act remained unclear. In the midst of today’s moods of identification, there are high stakes – and many clear motives – for either obscuring or attempting to pinpoint identity. Given this, the lack of clear motive for identity play seems significant; by not signifying, it holds open a space to rethink the limits of today’s moods of identification.
The DAOWO programme is devised by Ruth Catlow and Ben Vickers in collaboration with the Goethe-Institut London, and the State Machines programme. Its title is inspired by a paper written by artist, hacker and writer Rhea Myers called DAOWO – Decentralised Autonomous Organisation With Others
Blue Sausage Infant is the solo electronic project from Washington DC’s Chester Hawkins. Active on the live scene since the late 1980s, he’s shared the stage with touring and local luminaries, whose stylistic echoes radiate his own productions. Hints from prog, industrial, dark ambient, and noise all come across on BSI’s first LP release, Negative Space. Issued on Zeromoon in gorgeous packaging and colored 180-gram vinyl, Negative Space’s three tracks combine into a diverse snapshot of Hawkins’ musical creativity and expertise using a fair number of electronic and other diverse instruments (including electric toothbrush), all helpfully enumerated on the inner sleeve.

Side one is the single solo track “Motion Parallax,” a drifting space music riff that evolves through increasingly soupy accompaniments. From the Berlin overtones that emerge from the opening swirling white noise to a tribal electronic rhythm that reminded me of the proto-noise-punk band Chrome, BSI creates a diorama of timbral and harmonic landscapes. A distorted voice just out of comprehension earnestly and repeatedly strives, but fails to make herself meet and fuck understood, channeling an obscure Samuel Beckett character. Perhaps because of its murkiness, present even in the background of the rhythmic passages, Motion Parallax carries a lulling quality, a hard-edged long-form ambient work.
By contrast, side two opens considerably further towards krautrock with the title track, thanks to the assistance of a guitarist, a drummer, and a fourth performer on percussion and electronics. For all that side one referenced ambient, “Negative Space” draws from post-rock, with sustained guitar textures, rhythmic bass riffs, four-bar phrase structures, and a continuous dramatic build over the fourteen-minute performance. The side concludes with the shorter solo track “Subferal,” dense electronics dotted with sirens and alarms, led by an obsessive oscillation that starts on an intense single note and dissolves into swizzling distortion.
Originally posted on Furthernoise: http://www.furthernoise.org/index.php?url=page.php&ID=430&iss=96
In early February 2011, while researching the Japanese post-war economic miracle for a Biosphere project, Geir Jenssen found an old photo of Mihama nuclear plant. The site of this futuristic-looking plant in so lovely a spot by the sea intrigued him. Were they safe from earthquakes and tsunamis? Further reading revealed many to be in quake-prone areas, some even by shores hit by tsunamis previously. Narrowing focus to Japanese plants, he determined to soundtrack them – architecture and design, location, potential risk. N-Plants was finished on February 13th. A month later a friend wrote: ‘Geir, some time ago you asked for a photo of a Japanese nuclear powerplant …how did you actually predict the future?…’

Several months on, Jenssen’s prophetic words take on an eerie resonance, though the mood of N-Plants is far from the dystopian desolation one might have projected. A more ambiguous affair, it reveals itself less of an isolationist gloomfest than a collection of retro-futurist downtempo ambient house that seems to hark back to Biosphere’s early 90s IDM orientation circa Microgravity. The music, deceptively pretty, has about it a robotic undertone, its clipped rhythms of (deliberately?) low timbral interest, tones with a slightly degraded edge, a patina of peripheral hiss and whirr, slender hollowed out drones, as if to represent an alienated view of the still life of these structures, and aspects of their architecture and morality through a quasi-Ballardian sci-fi expressionist haze.

With its hissing effluvia and ominous chord thematics, “Joyo” is closest to the portent the theme might have evoked, but overall there’s a lightness of touch, eye to the bright visions of 60s sci-fi rendered via a slightly askew downtempo IDM. Sonics tap into the retro-future, signalling a certain remote sensed nostalgia. “Sendai-1″ sets the tone, a machine koan with Orientalist marimba-like sequences and a vacated drone at the core; the subsequent “Shika-1” and “Ikata-1” evoke a similar air of serenity with a clinical faintly sinister edge, blithe glaze-eyed synthetics and syncopated beats pulsing functionally under warmly wheezing pads.
But for all Jenssen’s precision sound design, N-Plants strikes as a little underdone and strangely lacking in musical, if not conceptual, substance, from a man responsible for one of the Top Ambient albums of all time, Substrata. Where that album memorably sounded depths, N-Plants scrolls somewhat dead-eyed over flat planes, as on the evacuated chiming recursions of “Fujiko”. Much of the album sounds almost like a decades-old artefact with its intermediate technology synth sounds and blank drum pads. This depletion is doubtless deliberate, sound signifying the faded scientific glory of its subject – tarnished future visions, modernist hopes, revealed as vainglorious hubris. N-Plants is truly a Music for Powerplants, in the way Eno’s was a Music For Airports. But, as with this latter, ideational heft doesn’t suffice to make it the best musical work of a master sonician.
Those seeking more musical meat may appreciate more fully fleshed out realizations from The Sight Below: